Free CompTIA XK0-006 Practice Questions 2026 - Page 2
System Management
A systems administrator needs to set the IP address of a new DNS server. Which of the following files should the administrator modify to complete this task?
A. /etc/whois.conf
B. /etc/resolv.conf
C. /etc/nsswitch.conf
D. /etc/dnsmasq.conf
Explanation:
The /etc/resolv.conf file is the primary configuration file for system DNS resolution. It specifies which DNS name servers the system should use for domain name resolution.
What /etc/resolv.conf does:
Defines the DNS servers (name servers) that the system queries
Sets search domains for hostname lookups
Configures resolver options and behavior
Read by the system's resolver library for all DNS queries
Typical /etc/resolv.conf content:
# Specify DNS servers (IP addresses)
nameserver 192.168.1.100
nameserver 8.8.8.8
nameserver 8.8.4.4
# Search domain for unqualified hostnames
search example.com lab.example.com
# Options
options timeout:2 attempts:3
To set the IP address of a new DNS server, the administrator would add or modify a line like:
nameserver 192.168.1.53
Why other options are incorrect:
❌ /etc/whois.conf
Purpose: Configuration file for the whois command
Function: Maps whois servers to specific domain extensions
Limitation: Only affects the whois client command, not system-wide DNS resolution
Rarely used and unrelated to system DNS configuration
❌ /etc/nsswitch.conf
Purpose: Name Service Switch configuration file
Function: Determines the order of sources for various system databases (hosts, passwd, group, services)
Limitation: Controls which services are queried (files, dns, ldap, etc.), not where the DNS servers are
Example entry: hosts: files dns - this tells the system to check /etc/hosts first, then DNS
Does NOT contain DNS server IP addresses
❌ /etc/dnsmasq.conf
Purpose: Configuration file for dnsmasq (DNS forwarder/DHCP server service)
Function: Configures the dnsmasq service if installed and running
Limitation: Only relevant if the system runs dnsmasq as a local DNS server
Even with dnsmasq, the system's resolver still uses /etc/resolv.conf (often pointing to localhost)
This is service-specific, not the system-wide resolver configuration
Reference:
man 5 resolv.conf - The manual page for resolv.conf format
The resolver is part of glibc and reads this file
Changes to /etc/resolv.conf take effect immediately for new connections
A DevOps engineer needs to create a local Git repository. Which of the following commands should the engineer use?
A. git init
B. git clone
C. git config
D. git add
Explanation:
The git init command is the standard way to initialize a brand-new, empty Git repository in a local directory.
Initialization:
When you run this command, Git creates a hidden subdirectory named .git that contains all the necessary metadata and skeleton files for version control tracking.
Local Workflow:
This is specifically used when starting a project from scratch on a local machine rather than downloading an existing project from a server.
Explanation of Incorrect Answers
git clone:
This command is used to copy an existing repository from a remote source (like GitHub or GitLab) to your local machine. While it results in a local repository, it is used for pre-existing projects rather than creating a new one from a local folder.
git config:
This utility is used to set configuration options, such as your username, email address, or editor preferences. It does not create or initialize a repository; it merely defines how Git behaves on your system.
git add:
The add command moves changes from the working directory to the staging area. You cannot use git add until a repository has already been initialized with git init or git clone.
Reference:
CompTIA Exam Objective: Domain 3.0 (Scripting, Containers, and Automation) – Subsection 3.3: "Explain version control concepts using Git."
Reference: Pro Git Book (Chacon & Straub); Official CompTIA Linux+ Study Guide, Chapter on Automation and Orchestration.
Which of the following best describes journald?
A. A system service that collects and stores logging data
B. A feature that creates crash dumps in case of kernel failure
C. A service responsible for keeping the filesystem journal
D. A service responsible for writing audit records to a disk
Explanation:
journald is part of the systemd suite. It is a daemon that collects, stores, and manages log data from the kernel, system services, and user applications.
Logs are stored in a binary journal format, which can be queried using the journalctl command.
This provides centralized, structured logging, making it easier to filter, search, and analyze system events.
Why the Other Options Are Wrong
A feature that creates crash dumps in case of kernel failure → That’s handled by kdump, not journald.
A service responsible for keeping the filesystem journal → That’s part of the filesystem itself (e.g., ext4 journaling), not journald.
A service responsible for writing audit records to a disk → That’s the role of auditd, not journald.
Reference:
Systemd documentation: journald is the logging service that stores logs in binary format and integrates with journalctl for querying.
CompTIA Linux+ XK0-006 Exam Objectives: Log Management and Monitoring (Domain: Security).
A DevOps engineer made some changes to files in a local repository. The engineer realizes that the changes broke the application and the changes need to be reverted back. Which of the following commands is the best way to accomplish this task?
A. git pull
B. git reset
C. git rebase
D. git stash
Explanation:
The engineer wants to revert changes made in a local repository because they broke the application.
The command best suited for undoing local changes and returning the repository to a previous state is:
git reset
What git reset does:
Moves the current branch (HEAD) back to a previous commit.
Can unstage files or completely discard changes depending on options.
Common usage:
git reset --hard HEAD
or
git reset --hard
This restores files to a known working state.
Why the Other Options Are Incorrect
❌ git pull
Fetches and merges changes from a remote repository.
Does not undo local changes.
❌ git rebase
Rewrites commit history to apply commits onto another base.
Not intended for reverting broken local changes.
❌ git stash
Temporarily saves changes for later use.
Does not revert repository back to a working version.
Linux+ XK0-006 Exam Tip
Quick Git recovery mapping:
Situation → Command
Undo local commits/changes → git reset ✅
Temporarily save work → git stash
Update from remote → git pull
Rewrite commit history → git rebase
Exam Keyword Trigger:
If you see “revert local changes” → think git reset.
Which of the following filesystems contains non-persistent or volatile data?
A. /boot
B. /usr
C. /proc
D. /var
Explanation:
The /proc directory is a pseudo-filesystem (often called a virtual filesystem) that serves as an interface to the Linux kernel and process information.
Non-Persistent/Volatile:
The data within /proc does not exist on any physical disk. Instead, it is generated "on the fly" by the kernel in the system's RAM.
System State:
It contains information about currently running processes (organized by PID) and hardware configuration (e.g., /proc/cpuinfo, /proc/meminfo).
Volatility:
Because it exists only in memory, all data in /proc is lost instantly when the system is powered down or rebooted.
Explanation of Incorrect Answers
/boot:
This directory contains the files needed to start the system, such as the Linux kernel, initramfs, and the GRUB bootloader configuration. This data is persistent and must be stored on a physical disk (usually a dedicated partition) to be available during the power-on self-test (POST) and boot process.
/usr:
The /usr (Unix System Resources) directory contains the majority of user utilities and applications (e.g., /usr/bin, /usr/lib). This is a read-only, persistent filesystem that holds static data installed by the package manager.
/var:
The /var directory is used for variable data that changes during system operation, such as logs (/var/log), mail, and print spools. While the data inside changes frequently, the directory itself is persistent and resides on a physical disk so that logs are preserved across reboots for troubleshooting.
Reference:
CompTIA Exam Objective: Domain 1.0 (System Management) – Subsection 1.1: "Summarize and utilize Linux command line tools" and "Manage the filesystem hierarchy."
Reference: Filesystem Hierarchy Standard (FHS); Official CompTIA Linux+ Study Guide, Chapter on Filesystem Management and Hierarchy.
Which of the following is a reason multiple password changes on the same day are not allowed?
A. To avoid brute-forced password attacks by making them too long to perform
B. To increase password complexity and the system's security
C. To stop users from circulating through the password history to return to the originally used password
D. To enforce using multifactor authentication with stronger encryption algorithms instead of passwords
Explanation:
In Linux and other enterprise systems, administrators often configure a password history policy (e.g., remember=5) to prevent users from reusing their favorite passwords. However, without a minimum password age (often set to 1 day or 24 hours), a user could bypass this restriction by changing their password multiple times in a single session—cycling through dummy passwords until the system's history limit is reached—and then resetting it back to the original password. Restricting multiple changes on the same day forces the user to keep each new password for a significant period, making this "cycling" tactic impractical.
Why other options are incorrect
❌ To avoid brute-forced password attacks by making them too long to perform:
Brute-force protection is typically handled by enforcing password complexity, minimum length, and account lockout thresholds after failed attempts, not by limiting the frequency of successful password changes.
❌ To increase password complexity and the system's security:
While complexity (uppercase, digits, symbols) increases security, the specific rule against multiple daily changes is a temporal restriction aimed at enforcing the history policy, not the inherent complexity of the characters used.
❌ To enforce using multifactor authentication with stronger encryption algorithms instead of passwords:
Password age policies are a legacy security measure for password-based authentication. They do not force a transition to MFA or change the underlying encryption algorithms (like SHA-512) used to store hashes in /etc/shadow.
Which of the following best describes the role of initrd?
A. It is required to connect to the system via SSH.
B. It contains basic kernel modules and drivers required to start the system.
C. It contains trusted certificates and secret keys of the system.
D. It is required to initialize a random device within a Linux system.
Explanation:
initrd (initial ramdisk) or initramfs (initial RAM filesystem) is a temporary filesystem used by the Linux kernel during the boot process before the real root filesystem is mounted. Its primary role is to provide essential modules and drivers needed to access the actual root filesystem.
What initrd/initramfs does:
Purpose:
Loads necessary drivers for hardware that isn't built directly into the kernel
Provides modules for storage controllers (SATA, SCSI, NVMe)
Contains filesystem drivers (ext4, XFS, Btrfs) to mount the real root
Includes LVM, RAID, or encryption modules if the root is on such volumes
Performs early userspace setup before switching to the real root
Boot process with initrd:
1. BIOS/UEFI → Bootloader (GRUB)
2. Bootloader loads kernel and initrd into memory
3. Kernel decompresses and starts, mounts initrd as temporary root
4. Kernel runs /init from initrd
5. initrd loads necessary modules and drivers
6. initrd mounts the real root filesystem
7. initrd performs pivot_root to switch to real root
8. Real init system (systemd) takes over
When initrd is essential:
Root on LVM: Needs LVM modules to activate volume groups
Root on encrypted disk: Needs crypto modules to unlock the drive
Root on network: Needs network drivers for NFS root
Root on uncommon hardware: Needs drivers for specialized storage controllers
Root on RAID: Needs MD RAID modules to assemble arrays
Why other options are incorrect:
❌ It is required to connect to the system via SSH.
SSH connectivity is managed by the SSH daemon (sshd) which runs AFTER the system has fully booted
SSH requires network configuration, which happens in the main system, not during early boot
initrd is long gone by the time SSH is available
SSH has nothing to do with the initial hardware detection and root mounting phase
❌ It contains trusted certificates and secret keys of the system.
Certificates and keys are typically stored in /etc/ssl/certs or /etc/ssh/ on the root filesystem
These are security credentials for services, not boot components
initrd is temporary and not designed for persistent secret storage
Some specific setups (like disk encryption) might include keys in initrd, but this is not its primary purpose
❌ It is required to initialize a random device within a Linux system.
The random device (/dev/random, /dev/urandom) is provided by the kernel, not initrd
Random number generation is a kernel feature that initializes independently
Some early boot entropy gathering might occur, but this is not the role of initrd
Reference:
initrd = Initial RAM Disk
initramfs = Initial RAM Filesystem (modern replacement)
Required when kernel lacks built-in drivers for boot hardware
Created by tools like mkinitramfs (Debian) or dracut (RHEL/Fedora)
Without initrd, the kernel would need every possible driver compiled in, making the kernel huge
A Linux administrator wants to add a user to the Docker group without changing the user’s primary group.
Which of the following commands should the administrator use to complete this task?
A. sudo groupmod docker user
B. sudo usermod -g docker user
C. sudo usermod -aG docker user
D. sudo groupmod -G docker user
Explanation:
To add a user to a supplementary group like docker without affecting their primary group, the -a (append) and -G (groups) flags are required. The -a flag is critical because it ensures the user is added to the new group while remaining a member of all their current secondary groups. Without it, the user would be removed from any other existing secondary groups.
Why other options are incorrect
❌ sudo groupmod docker user:
The groupmod command is used to modify the properties of the group itself (such as its name or GID), not to manage user membership within that group.
❌ sudo usermod -g docker user:
The lowercase -g flag changes the user's primary group. This would violate the requirement to add the user to the group without changing their primary group assignment.
❌ sudo groupmod -G docker user:
The groupmod command does not support a -G flag for adding users. As mentioned, this utility is intended for group metadata, not membership administration.
A Linux administrator is testing a web application on a laboratory service and needs to temporarily allow DNS and HTTP/HTTPS traffic from the internal network. Which of the following commands will accomplish this task?
A. firewalld -- add-service=dns, http,https -- zone=internal
B. iptables -- enable-service='dns|http|https' -- zone=internal
C. firewall-cmd --add-service={dns, http, https} --zone=internal
D. systemctl mask firewalld --for={dns, http, https} --zone=internal
Explanation:
The administrator wants to temporarily allow DNS, HTTP, and HTTPS traffic using firewalld.
The correct command uses firewall-cmd, which is the proper management tool for firewalld rules:
firewall-cmd --add-service={dns,http,https} --zone=internal
Why this works
--add-service allows predefined services.
{dns,http,https} adds multiple services at once.
--zone=internal applies rules only to the internal network zone.
Without --permanent, the change is temporary (lost after reboot), matching the requirement.
❌ Why the Other Options Are Incorrect
❌ firewalld -- add-service=...
firewalld is a daemon/service, not the configuration command.
Invalid syntax.
❌ iptables -- enable-service=...
iptables does not use service names or zones.
firewalld abstracts iptables rules.
Invalid command.
❌ systemctl mask firewalld ...
mask disables a service entirely.
Would block firewall operation, not allow traffic.
🧠 Linux+ XK0-006 Exam Tip
Key firewalld commands:
Task Command
Temporary allow service firewall-cmd --add-service= ✅
Permanent rule add --permanent
Reload rules firewall-cmd --reload
List rules firewall-cmd --list-all
💡 Exam keyword trigger:
If question says temporary firewall change, do NOT include --permanent.
While hardening a system, an administrator runs a port scan with Nmap, which returned the following output:
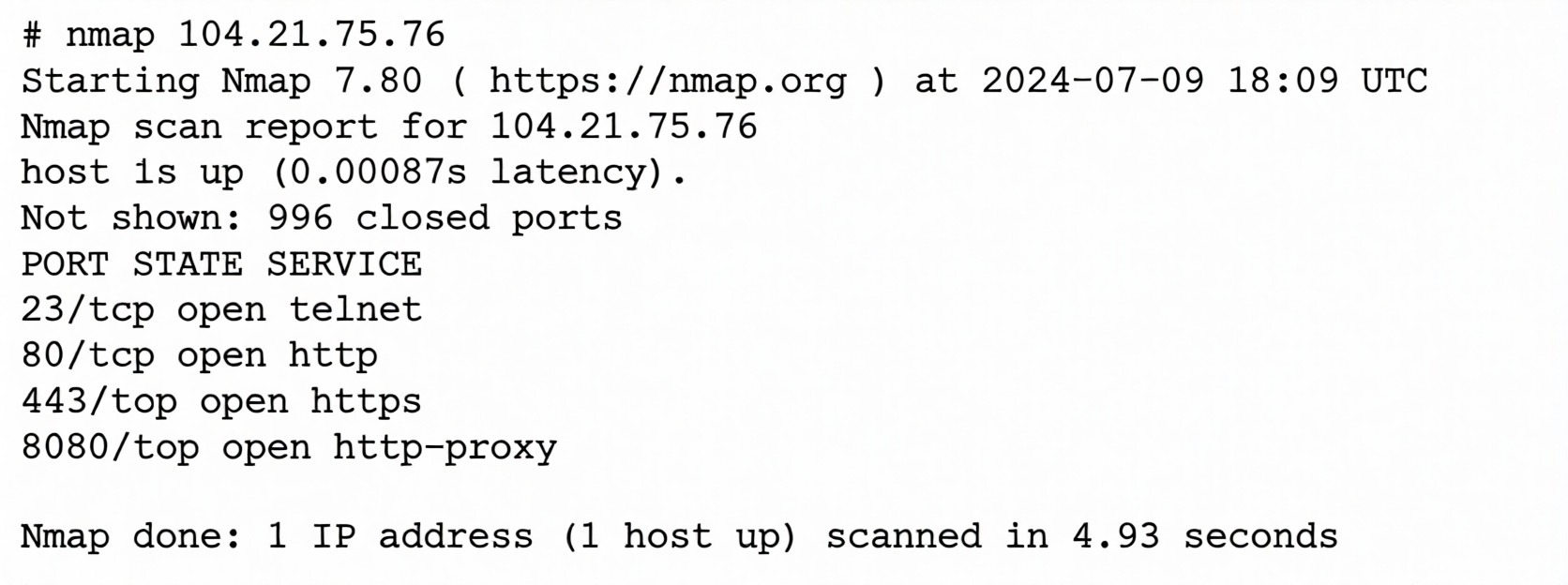
Which of the following is the best way to address this security issue?
A. Configuring a firewall to block traffic on port 23 on the server
B. Changing the system administrator's password to prevent unauthorized access
C. Closing port 80 on the network switch to block traffic
D. Disabling and removing the Telnet service on the server
Explanation:
The Nmap scan reveals that port 23 (telnet) is open on the server. Telnet is an outdated, insecure protocol that transmits all data, including login credentials, in cleartext (unencrypted). This presents a significant security vulnerability.
Analysis of the Nmap output:
PORT STATE SERVICE
23/tcp open telnet # ⚠️ INSECURE - transmits in cleartext
80/tcp open http # Web server (can be secure with HTTPS)
443/tcp open https # Secure web server (encrypted)
8080/tcp open http-proxy # Alternative web port
Why Telnet is a security risk:
No encryption: All data (including usernames and passwords) sent in plaintext
Can be intercepted: Anyone on the network can sniff credentials
No integrity checking: Data can be modified in transit
Outdated protocol: Modern alternatives provide encryption
Common attack vector: Frequently targeted by attackers
The best remediation:
Disabling and removing the Telnet service addresses the root cause by eliminating the vulnerable service entirely. This is a complete and permanent solution.
Why other options are incorrect:
❌ Configuring a firewall to block traffic on port 23 on the server
This is a workaround, not a fix
The Telnet service would still be running and could be:
* Re-enabled by accident
* Accessed if firewall rules change or fail
* Accessed from localhost (bypassing firewall)
Leaves unnecessary software installed (increases attack surface)
Better to remove the service entirely (defense in depth)
❌ Changing the system administrator's password to prevent unauthorized access
Does NOT address the vulnerability
Passwords sent via Telnet are still exposed in cleartext
Attackers can sniff the new password just as easily
Focuses on credential strength, not the insecure protocol
❌ Closing port 80 on the network switch to block traffic
Wrong port: Port 80 (HTTP) is not the security issue
Port 80 is legitimate web traffic
Blocking at the switch is network-level, not system hardening
Doesn't address the Telnet vulnerability at all
Would break legitimate web services
Secure Alternatives to Telnet:
Protocol Port Encryption Use Case
SSH 22 ✅ Yes Secure remote shell access
SCP/SFTP 22 ✅ Yes Secure file transfer
HTTPS 443 ✅ Yes Secure web access
To properly secure the system:
# 1. Stop the Telnet service immediately
sudo systemctl stop telnet.socket
sudo systemctl stop telnet.service
# 2. Disable Telnet from starting on boot
sudo systemctl disable telnet.socket
sudo systemctl disable telnet.service
# 3. Remove Telnet packages entirely
# On RHEL/CentOS/Fedora:
sudo dnf remove telnet-server telnet
# On Debian/Ubuntu:
sudo apt remove telnetd telnet
# 4. Ensure SSH is installed and properly configured
sudo systemctl enable --now sshd
# 5. Verify the port is closed
nmap localhost
# or
ss -lnt | grep :23
Security Best Practices:
Principle of Least Functionality: Remove or disable unnecessary services
Defense in Depth: Multiple layers of security (remove service + firewall)
Encrypt Everything: Use encrypted protocols (SSH instead of Telnet)
Regular Audits: Periodic port scans to detect open ports
Service Management: Only run services that are required
Reference:
Telnet (RFC 854) - No encryption, credentials in plaintext
NIST Guidelines: Remove or disable unnecessary network services
CIS Benchmarks: Recommend disabling Telnet and using SSH instead
PCI DSS Requirement 2.2.2: Disable all insecure services and protocols
| Page 2 out of 15 Pages |
