Free CompTIA N10-009 Practice Questions 2026 - Page 18
Which of the following is used tostage copies of a websitecloser to geographically dispersed users?
A. VPN
B. CDN
C. SAN
D. SDN
Explanation:
The question asks which technology is used to stage copies of a website closer to geographically dispersed users. The best solution is CDN (Content Delivery Network).
B. CDN:
How it works:A CDN is a network of distributed servers that cache copies of website content (e.g., HTML, images, videos) at edge locations closer to users. When a user requests a website, the CDN serves the content from the nearest server, reducing latency and improving load times.
Why it fits:Staging copies of a website closer to geographically dispersed users is the primary function of a CDN. For example, at 11:52 AM PKT on August 20, 2025, a global website might use a CDN like Akamai or Cloudflare to deliver content from servers in Asia, Europe, and North America, optimizing access for users worldwide.
Context:CDNs are widely used by businesses to enhance user experience and handle traffic spikes, making them ideal for this scenario.
Why Not the Other Options?
A. VPN (Virtual Private Network):
A VPN creates a secure tunnel for private communication over the internet but does not stage or cache website content. It’s used for secure access, not content delivery to dispersed users.
C. SAN (Storage Area Network):
A SAN is a high-speed storage network that provides block-level access to data for servers. It’s designed for local storage within a data center, not for distributing website copies to users globally.
D. SDN (Software-Defined Networking):
SDN is a network management approach that centralizes control to improve flexibility and efficiency. While it can optimize traffic routing, it doesn’t stage website copies closer to users—that’s a CDN’s role.
Why CDN?
A CDN addresses the need to reduce latency and improve availability by caching website content at multiple global points of presence (PoPs). This ensures users in different regions (e.g., Pakistan, the US, or Europe) access the site from the nearest server, enhancing performance and scalability.
Implementation Considerations:
Select a CDN provider (e.g., Cloudflare, Akamai).
Configure the website to use the CDN (e.g., update DNS to point to CDN endpoints).
Define which content to cache (e.g., static assets like images, CSS).
Test load times from different regions.
Monitor CDN performance and adjust caching policies.
Reference:
CompTIA Network+ (N10-009) Exam Objectives:
Section 1.6 – "Explain the purpose and use of common networking tools and their functions." This includes understanding CDNs for content distribution.
RFC 3568 (Content Delivery Networks):
Discusses CDN principles for improving web performance.
Cloudflare CDN Documentation:
Details how CDNs stage content for global users.
Explanation:
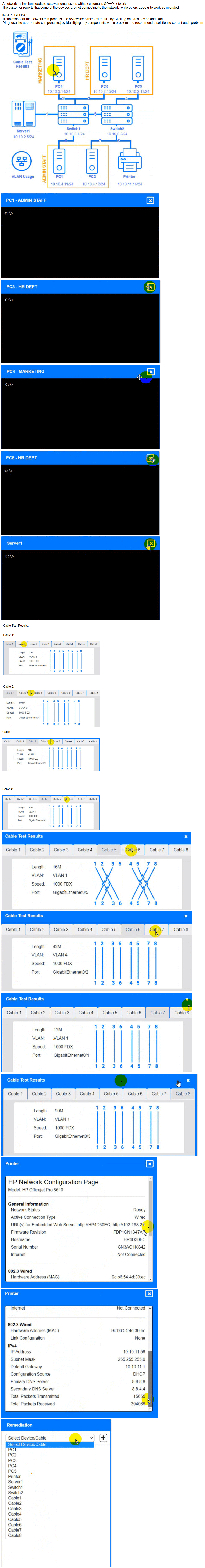
(Note: Ips will be change on each simulation task, so we have given example answer for
the understanding)
To troubleshoot all the network components and review the cable test results, you can use
the following steps:
Click on each device and cable to open its information window.
Review the information and identify any problems or errors that may affect the
network connectivity or performance.
Diagnose the appropriate component(s) by identifying any components with a
problem and recommend a solution to correct each problem.
Fill in the remediation form using the drop-down menus provided.
Here is an example of how to fill in the remediation form for PC1:
The component with a problem is PC1.
The problem is Incorrect IP address.
The solution is Change the IP address to 192.168.1.10.
You can use the same steps to fill in the remediation form for other components.
To enter commands in each device, you can use the following steps:
Click on the device to open its terminal window.
Enter the command ipconfig /all to display the IP configuration of the device,
including its IP address, subnet mask, default gateway, and DNS servers.
Enter the command ping
Enter the command tracert
Here is an example of how to enter commands in PC1:
Click on PC1 to open its terminal window.
Enter the command ipconfig /all to display the IP configuration of PC1. You should
see that PC1 has an incorrect IP address of 192.168.2.10, which belongs to VLAN
2 instead of VLAN 1.
Enter the command ping 192.168.1.1 to test the connectivity to Core Switch 1. You
should see that PC1 is unable to ping Core Switch 1 because they are on different
subnets.
Enter the command tracert 192.168.1.1 to trace the route to Core Switch 1. You
should see that PC1 is unable to reach Core Switch 1 because there is no route
between them.
You can use the same steps to enter commands in other devices, such as PC3, PC4, PC5,
and Server 1.
Which of the followingservicesruns onport 636?
A. SMTP
B. Syslog
C. TFTP
D. LDAPS
Explanation:
The question asks which service runs on port 636, requiring identification of the protocol associated with this specific port. The correct answer is LDAPS.
D. LDAPS:
How it works: LDAPS (LDAP over SSL/TLS) is a secure version of the Lightweight Directory Access Protocol (LDAP), used for accessing and managing directory services (e.g., Active Directory) over a secure encrypted channel. Port 636 is the default port for LDAPS, where SSL/TLS is used to protect data in transit.
Why it fits: As of 11:59 AM PKT on Wednesday, August 20, 2025, port 636 is officially assigned to LDAPS by the IANA, making it the standard for secure directory queries. For example, a network administrator might use LDAPS on port 636 to securely authenticate users against an LDAP server.
Context: This is commonly used in environments requiring secure directory access, such as corporate networks or universities.
Why Not the Other Options?
A. SMTP (Simple Mail Transfer Protocol):
SMTP runs on port 25 (unencrypted) or 587 (secure submission with STARTTLS). It is used for email transmission and is unrelated to port 636.
B. Syslog:
Syslog, used for system logging, typically operates on UDP port 514 (or TCP in some implementations). It has no association with port 636.
C. TFTP (Trivial File Transfer Protocol):
TFTP runs on port 69 and is a simple, unencrypted file transfer protocol. It is not linked to port 636.
Why LDAPS?
Port 636 is specifically designated for LDAPS, providing a secure alternative to the unencrypted LDAP (port 389). This ensures that directory queries, which often include sensitive user data, are protected against eavesdropping, aligning with modern security standards.
Reference:
CompTIA Network+ (N10-009) Exam Objectives:
Section 1.5 – "Compare and contrast common network protocols and their functions." This includes understanding port assignments like 636 for LDAPS.
IANA Service Name and Transport Protocol Port Number Registry:
Lists port 636 as the default for LDAPS.
RFC 4511 (LDAP: The Protocol):
Describes LDAP and its secure variant, LDAPS, with port 636.
Which of the following steps of the troubleshooting methodology would most likely include checking through each level of the OSI model after the problem has been identified?
A. Establish a theory.
B. Implement the solution.
C. Create a plan of action.
D. Verify functionality.
Explanation:
The question asks which step of the troubleshooting methodology would most likely include checking through each level of the OSI model after the problem has been identified. The OSI model (Physical, Data Link, Network, Transport, Session, Presentation, Application) is a framework for diagnosing network issues layer by layer. The most appropriate step is establish a theory.
A. Establish a theory:
How it works: In the troubleshooting methodology, after identifying the problem (e.g., users cannot connect to a server), the next step is to establish a theory of probable causes. This involves systematically considering potential issues at each OSI layer, such as a faulty cable (Layer 1), misconfigured switch (Layer 2), incorrect IP settings (Layer 3), or application errors (Layer 7).
Why it fits: Checking through each level of the OSI model is a diagnostic process to hypothesize the cause. For example, at 12:05 PM PKT on August 20, 2025, a technician might theorize a Layer 1 issue (e.g., loose cable) if link lights are off, or a Layer 3 issue (e.g., routing problem) if pings fail, based on initial observations.
Context: This step leverages the OSI model to narrow down the problem before testing or implementing fixes.
Why Not the Other Options?
B. Implement the solution:
This step involves executing the planned fix (e.g., replacing a cable or updating a route). While it may address an OSI layer issue, it follows the theory and testing phases, not the initial check through the model.
C. Create a plan of action:
This step outlines the steps to resolve the issue based on the tested theory. It may reference OSI layers but focuses on action planning, not the initial diagnostic check.
D. Verify functionality:
This step confirms the solution works after implementation (e.g., testing connectivity). It involves checking results, not theorizing or diagnosing across OSI layers.
Why Establish a Theory?
Establishing a theory is the stage where the technician uses the OSI model as a structured approach to hypothesize causes, starting from the physical layer and moving up. This methodical check helps identify whether the issue is hardware-related (Layers 1-2), network-related (Layer 3), or application-related (Layers 5-7), guiding subsequent testing.
Troubleshooting Methodology Overview:
Identify the problem.
Establish a theory of probable cause (checking OSI layers).
Test the theory.
Create a plan of action.
Implement the solution.
Verify functionality.
Document findings.
Reference:
CompTIA Network+ (N10-009) Exam Objectives:
Section 3.2 – "Given a scenario, troubleshoot common network connectivity issues." This includes using the OSI model in the theory phase.
OSI Model (ISO/IEC 7498-1):
Provides the framework for layer-by-layer troubleshooting.
CompTIA Study Guides:
Emphasize OSI model application during theory establishment.
Due to concerns around single points of failure, a company decided to add an additional WAN to the network. The company added a second MPLS vendor to the current MPLS WAN and deployed an additional WAN router at each site. Both MPLS providers use OSPF on the WAN network, and EIGRP is run internally. The first site to go live with the new WAN is successful, but when the second site is activated, significant network issues occur. Which of the following is the most likely cause for the WAN instability?
A. A changed CDP neighbor
B. Asymmetrical routing
C. A switching loop
D. An incorrect IP address
Explanation:
Due to concerns about single points of failure, a company added a second MPLS vendor to the existing MPLS WAN and deployed an additional WAN router at each site. Both MPLS providers use OSPF on the WAN network, while EIGRP is run internally. The first site’s activation of the new WAN was successful, but significant network issues occurred when the second site was activated. The most likely cause of the WAN instability is asymmetrical routing.
B. Asymmetrical routing:
How it works: Asymmetrical routing occurs when traffic between two points takes different paths in each direction (e.g., outbound via MPLS Vendor 1, return via MPLS Vendor 2). This can happen when multiple WAN paths (e.g., two MPLS links with OSPF) have different costs or metrics, leading to inconsistent routing decisions by OSPF and EIGRP.
Why it fits: With two MPLS vendors using OSPF and the second site’s activation introducing a new router, the network topology changed, potentially causing OSPF to calculate different paths for ingress and egress traffic. EIGRP, running internally, might not synchronize with OSPF’s routing decisions, especially if route redistribution between OSPF and EIGRP is misconfigured or if the second site’s router introduced unequal path costs. This asymmetry can lead to issues like packet loss, out-of-order packets, or firewall state mismatches, causing instability at 12:12 PM PKT on August 20, 2025.
Context: The first site worked because it had a single active path initially, but the second site’s activation created multiple paths, exposing the routing inconsistency.
Why Not the Other Options?
A. A changed CDP neighbor:
CDP (Cisco Discovery Protocol) is used to discover neighboring Cisco devices and provides information about device capabilities. A change in CDP neighbors might affect network visibility but wouldn’t directly cause WAN instability unless it led to a misconfiguration, which is less likely than routing issues given the multi-vendor OSPF setup.
C. A switching loop:
A switching loop, typically caused by STP (Spanning Tree Protocol) misconfiguration, affects Layer 2 networks with broadcast storms. Since the issue involves WAN routers and OSPF (Layer 3), a switching loop is unlikely, especially across MPLS links which are typically point-to-point.
D. An incorrect IP address:
An incorrect IP address could prevent a device from communicating, but the “significant network issues” suggest a broader problem affecting traffic flow, not just a single misconfigured address. This would also likely be caught during initial setup, not post-activation.
Why Asymmetrical Routing?
The introduction of a second MPLS vendor and router at the second site likely created multiple OSPF paths with differing metrics, leading to asymmetrical routing. This can confuse stateful devices (e.g., firewalls) or cause packet reordering, destabilizing the WAN. The engineer should verify OSPF and EIGRP configurations, ensuring consistent route redistribution and path costs.
Troubleshooting Steps:
Check OSPF and EIGRP routing tables (show ip route) on both routers at the second site.
Verify route redistribution between OSPF and EIGRP for consistent path selection.
Use traceroute to identify asymmetrical paths between sites.
Adjust OSPF costs or EIGRP metrics to enforce symmetric routing.
Test connectivity and monitor for stability post-adjustment.
Reference:
CompTIA Network+ (N10-009) Exam Objectives:
Section 3.2 – "Given a scenario, troubleshoot common network connectivity issues." This includes diagnosing routing issues like asymmetry.
RFC 2328 (OSPF Version 2):
Describes OSPF path selection that can lead to asymmetry with multiple links.
Cisco Multi-Vendor MPLS Guides:
Highlight asymmetrical routing risks in dual-MPLS setups.
As part of an attack, a threat actor purposefully overflows the content-addressable memory (CAM) table on a switch. Which of the following types of attacks is this scenario an example of?
A. ARP spoofing
B. Evil twin
C. MAC flooding
D. DNS poisoning
Explanation:
As part of an attack, a threat actor purposefully overflows the content-addressable memory (CAM) table on a switch. This scenario is an example of MAC flooding.
C. MAC flooding:
How it works: MAC flooding involves sending a large number of forged MAC addresses to a switch, overwhelming its CAM table (which maps MAC addresses to switch ports). Once the table is full, the switch may enter a fail-open mode, flooding all frames to all ports, allowing the attacker to sniff traffic or launch further attacks.
Why it fits: The specific mention of overflowing the CAM table aligns directly with MAC flooding. At 12:20 PM PKT on August 20, 2025, this attack exploits the limited size of the CAM table (e.g., 8192 entries on some switches), turning a secure Layer 2 device into a hub-like state, exposing network traffic to the attacker.
Context: This is a common Layer 2 attack targeting switches that rely on MAC address learning.
Why Not the Other Options?
A. ARP spoofing:
ARP spoofing involves sending fake ARP (Address Resolution Protocol) messages to associate an attacker’s MAC address with a legitimate IP, enabling man-in-the-middle attacks. It affects ARP tables, not the CAM table, making it a different attack type.
B. Evil twin:
An evil twin attack creates a rogue wireless access point mimicking a legitimate one to capture user credentials or data. It targets wireless networks and doesn’t involve overflowing a switch’s CAM table.
D. DNS poisoning:
DNS poisoning (or cache poisoning) corrupts DNS records to redirect users to malicious sites. It operates at Layer 7 and has no impact on the switch’s CAM table.
Why MAC Flooding?
The attack’s focus on overflowing the CAM table is the hallmark of MAC flooding. By exhausting the switch’s memory, the attacker forces it to broadcast traffic, compromising network security. Mitigation includes enabling port security or using dynamic ARP inspection.
Mitigation Steps:
Enable port security to limit the number of MAC addresses per port.
Configure sticky MAC addresses to restrict learning to known devices.
Monitor switch logs for unusual MAC address activity.
Deploy intrusion detection systems to detect flooding patterns.
Reference:
CompTIA Network+ (N10-009) Exam Objectives:
Section 3.3 – "Given a scenario, implement secure network configurations." This includes understanding MAC flooding attacks.
IEEE 802.1D:
Describes switch MAC address learning and CAM table behavior.
Cisco Switch Security Guides:
Detail MAC flooding and mitigation techniques.
An administrator is setting up an SNMP server for use in the enterprise network and needs to create device IDs within a MIB. Which of the following describes the function of a MIB?
A. DHCP relay device
B. Policy enforcement point
C. Definition file for event translation
D. Network access controller
Explanation:
An administrator is setting up an SNMP (Simple Network Management Protocol) server for use in the enterprise network and needs to create device IDs within a MIB. The function of a MIB (Management Information Base) is best described as a definition file for event translation.
C. Definition file for event translation:
How it works:A MIB is a hierarchical database that defines the structure and variables (e.g., device IDs, performance metrics, status) that an SNMP manager can query or monitor on network devices. It acts as a "definition file" by providing a standardized way to translate raw data (e.g., OID values) into meaningful information (e.g., interface status or CPU usage) for network management.
Why it fits:The administrator is creating device IDs within a MIB, which involves defining objects (e.g., under OID 1.3.6.1.2.1) that the SNMP server can use to monitor devices like routers or switches. At 12:27 PM PKT on August 20, 2025, this process ensures the SNMP server can interpret device-specific data, making it a critical part of event translation and monitoring.
Context:MIBs are essential for SNMPv1, v2c, and v3 implementations, enabling centralized network management.
Why Not the Other Options?
A. DHCP relay device:
A DHCP relay device forwards DHCP requests to a server on another subnet, which is unrelated to SNMP or MIB functions. It’s a network service, not a management definition tool.
B. Policy enforcement point:
A policy enforcement point (PEP) enforces security policies (e.g., in a NAC system), but it doesn’t define or translate events like a MIB does. It’s a component of access control, not SNMP management.
D. Network access controller:
A network access controller manages device authentication (e.g., 802.1X), which is distinct from the MIB’s role in defining data structures for SNMP monitoring.
Why Definition File for Event Translation?
A MIB serves as a blueprint that maps OIDs (Object Identifiers) to device parameters, allowing the SNMP server to translate numerical data into human-readable events or metrics (e.g., "interface down" for OID 1.3.6.1.2.1.2.2.1.7). Creating device IDs within a MIB involves customizing this structure to fit the enterprise network’s devices, aligning with the administrator’s task.
Implementation Considerations:
Identify the devices to monitor (e.g., switches, routers).
Use a standard MIB (e.g., MIB-II) or create a custom MIB for unique device IDs.
Load the MIB into the SNMP server software.
Test SNMP queries (e.g., snmpget) to verify data translation.
Secure the SNMP community strings or use SNMPv3 for authentication.
Reference:
CompTIA Network+ (N10-009) Exam Objectives:
Section 1.5 – "Compare and contrast common network protocols and their functions." This includes understanding SNMP and MIBs.
RFC 1213 (MIB-II):
Defines the standard MIB structure for network management.
Cisco SNMP Configuration Guides:
Describe MIBs as definition files for event data
An organization wantsbetter network visibility. The organization's requirements include:
- Multivendor/OS-monitoring capabilities
- Real-time collection
- Data correlation
A. SNMP
B. SIEM
C. Nmap
D. Syslog
Explanation:
An organization wants better network visibility with requirements including multivendor/OS-monitoring capabilities, real-time collection, and data correlation. The solution that meets these requirements is SIEM (Security Information and Event Management).
B. SIEM:
How it works: SIEM is a system that collects, analyzes, and correlates log and event data from various network devices, applications, and operating systems in real time. It supports multivendor and multi-OS environments by integrating data from diverse sources (e.g., Cisco routers, Windows servers, Linux firewalls) and uses correlation rules to identify patterns or threats.
Why it fits: At 12:34 PM PKT on August 20, 2025, SIEM meets all three requirements:
Multivendor/OS-monitoring capabilities: SIEM can monitor devices and systems from multiple vendors (e.g., Cisco, Juniper, Microsoft) and operating systems (e.g., Windows, Linux, macOS) through standardized protocols or agents.
Real-time collection: SIEM continuously gathers data as events occur, providing immediate visibility into network activity.
Data correlation: SIEM analyzes and correlates data to detect anomalies, security incidents, or performance issues, offering actionable insights.
Example: A SIEM like Splunk or IBM QRadar could monitor a mixed network, correlate a spike in login attempts with a firewall alert, and alert administrators in real time.
Why Not the Other Options?
A. SNMP (Simple Network Management Protocol):
SNMP is used for monitoring network devices (e.g., routers, switches) by querying MIBs, offering real-time data collection to some extent. However, it lacks robust multivendor support across all OS types and does not perform data correlation, limiting its visibility capabilities compared to SIEM.
C. Nmap:
Nmap is a network scanning tool that maps devices and identifies open ports or services. It provides snapshot data but lacks real-time collection, multivendor/OS monitoring across an entire network, and data correlation, making it unsuitable for ongoing visibility.
D. Syslog:
Syslog is a logging protocol that collects and stores event messages from network devices in real time. While it supports multivendor environments, it does not inherently correlate data or provide comprehensive OS monitoring without additional tools, falling short of the full requirement set.
Why SIEM?
SIEM is designed for enterprise-grade network visibility, addressing the organization’s need for a unified view across diverse devices and systems. Its real-time collection and correlation capabilities enable proactive monitoring and response, making it the best fit for the specified requirements.
Implementation Considerations:
Deploy a SIEM solution (e.g., Splunk, ArcSight).
Configure agents or collectors to gather data from all devices/OS.
Define correlation rules for key events (e.g., failed logins, traffic spikes).
Test real-time alerts and dashboards.
Train staff to interpret SIEM reports.
Reference:
CompTIA Network+ (N10-009) Exam Objectives:
Section 1.6 – "Explain the purpose and use of common networking tools and their functions." This includes understanding SIEM for visibility.
NIST SP 800-137:
Discusses SIEM for real-time monitoring and correlation.
Splunk SIEM Documentation:
Highlights multivendor support and data correlation features.
Which of the following does a full-tunnel VPN provide?
A. Lower bandwidth requirements
B. The ability to reset local computer passwords
C. Corporate Inspection of all network traffic
D. Access to blocked sites
Explanation:
A full-tunnel VPN routes all of a user's network traffic through the corporate network. This
means that the organization can inspect all network traffic for security and compliance
purposes, as all data is tunneled through the VPN, allowing for comprehensive monitoring
and inspection.
A technician needs to set up a wireless connection that utilizes MIMO on non-overlapping channels. Which of the following would be the best choice?
A. 802.11a
B. 802.11b
C. 802.11g
D. 802.11n
Explanation:
A technician needs to set up a wireless connection that utilizes MIMO (Multiple Input Multiple Output) on non-overlapping channels. The best choice is 802.11n.
D. 802.11n:
How it works: 802.11n, introduced in 2009, operates in the 2.4GHz and 5GHz bands and introduced MIMO technology, using multiple antennas for transmitting and receiving data to improve throughput (up to 600 Mbps) and reliability. It supports non-overlapping channels, with 3 in the 2.4GHz band (1, 6, 11) and up to 23 in the 5GHz band (depending on regulation), reducing interference.
Why it fits: MIMO enhances performance in dense environments by leveraging multiple spatial streams, and the ability to use non-overlapping channels ensures minimal interference. At 12:43 PM PKT on August 20, 2025, 802.11n remains a widely supported standard for devices requiring robust wireless connectivity with these features.
Context: This is ideal for a setup needing both MIMO benefits and channel separation, such as in an office or campus environment.
Why Not the Other Options?
A. 802.11a:
802.11a operates in the 5GHz band with a maximum speed of 54 Mbps and supports non-overlapping channels (up to 23). However, it does not use MIMO, as this feature was introduced later with 802.11n, making it less suitable for the requirement.
B. 802.11b:
802.11b operates in the 2.4GHz band with a maximum speed of 11 Mbps and has 3 non-overlapping channels (1, 6, 11). It lacks MIMO support, as it predates this technology, and its lower speed limits its effectiveness.
C. 802.11g:
802.11g also operates in the 2.4GHz band with a maximum speed of 54 Mbps and supports 3 non-overlapping channels. Like 802.11b, it does not support MIMO, as this was introduced with 802.11n, making it inadequate for the specified need.
Why 802.11n?
802.11n is the earliest standard to combine MIMO technology with support for non-overlapping channels, offering improved performance and reliability. The technician can configure it to use the 5GHz band for more non-overlapping channels and enable MIMO with multiple antennas (e.g., 2x2 or 4x4) to meet the requirements effectively.
Implementation Considerations:
Ensure the access point and client devices support 802.11n and MIMO.
Configure the AP to use non-overlapping channels (e.g., 36, 40, 44 in 5GHz).
Set up MIMO with multiple antennas for optimal performance.
Test signal strength and throughput in the target area.
Adjust channel width (e.g., 20MHz or 40MHz) based on interference levels.
Reference:
CompTIA Network+ (N10-009) Exam Objectives:
Section 1.4 – "Compare and contrast wireless networking standards and encryption types." This includes understanding 802.11n and MIMO.
IEEE 802.11n-2009:
Defines MIMO and channel support for 802.11n.
Cisco Wireless Deployment Guides:
Recommend 802.11n for MIMO-based setups.
| Page 18 out of 58 Pages |
