Free CompTIA DS0-001 Practice Questions 2026 - Page 2
Which of the following have data manipulation and procedural scripting power? (Choose two.)
A. PQL
B. PL/SQL
C. Advanced
D. SQL
E. SQL
F. T-SQL
F. T-SQL
Explanation:
To address the requirement for procedural scripting power alongside data manipulation, a language must go beyond standard SQL. While standard SQL is declarative (telling the database what to do), procedural extensions allow for logic (telling the database how to do it using loops, variables, and conditions).
Why PL/SQL and T-SQL are Correct
B. PL/SQL (Procedural Language/Structured Query Language):
This is Oracle Corporation's proprietary extension for the Oracle Database. It provides procedural capabilities such as constants, variables, procedures, functions, and exception handling, allowing developers to wrap complex business logic within the database itself.
F. T-SQL (Transact-SQL):
This is Microsoft’s and Sybase's proprietary extension to SQL used in Microsoft SQL Server. Like PL/SQL, it includes procedural programming elements like local variables and various support functions for string processing, date processing, and mathematics.
Why Other Options are Incorrect
A. PQL:
This generally refers to "Process Query Language" or other niche languages not standard to the CompTIA DataSys+ curriculum for general-purpose procedural scripting.
D & E. SQL:
Standard SQL (Structured Query Language) is primarily a declarative language used for data retrieval and manipulation. By itself, standard SQL lacks the procedural "scripting power" (like IF...ELSE logic or WHILE loops) found in its proprietary extensions.
C. Advanced:
This is a descriptive term, not a specific database language or engine.
References
CompTIA DataSys+ (DS0-001) Objective 1.3: "Explain the use of common SQL statements." This objective requires candidates to understand the differences between standard SQL and procedural extensions like T-SQL and PL/SQL for automation and complex tasks.
A database administrator needs to provide access to data from two different tables to multiple group users in order to facilitate ongoing reporting. However, some columns in each table are restricted, and users should not be able to see the values in these columns. Which of the following is thebestaction for the administrator to take?
A. Create a stored procedure.
B. Create a view.
C. Create a csv export.
D. Create a trigger.
Explanation:
In database security and administration, a view acts as a virtual table that presents the results of a predefined query. It is the industry-standard method for providing controlled access to data while maintaining security.
Why a View is the Best Action
Column-Level Security: A view allows the administrator to explicitly select only the non-restricted columns from the source tables. Users see the data they need, while the restricted columns remain completely hidden.
Data Aggregation: Views can easily perform joins across "two different tables," presenting them as a single object for "ongoing reporting".
Simplicity for End Users: Instead of writing complex join queries themselves, users simply run a SELECT against the view name, ensuring consistency in reporting across the group.
Why Other Options are Incorrect
A. Create a stored procedure:
While a stored procedure can return data, its primary purpose is to execute a sequence of programmatic steps or logic. Using it for simple reporting adds unnecessary complexity compared to a view.
C. Create a csv export:
This creates a static, point-in-time file. It does not facilitate "ongoing" reporting because the file would become outdated immediately as the database updates. It also creates a security risk by moving data into an unmanaged flat file.
D. Create a trigger:
A trigger is an automated action that runs in response to an event (like INSERT or DELETE). It cannot be used to provide or filter read-access for users.
References
CompTIA DataSys+ (DS0-001) Objective 1.2: "Explain the use of common database objects." This includes the definition and use cases for tables and views.
A database administrator wants to remove inactive customers from a database. Which of
the following statements should the administrator use?
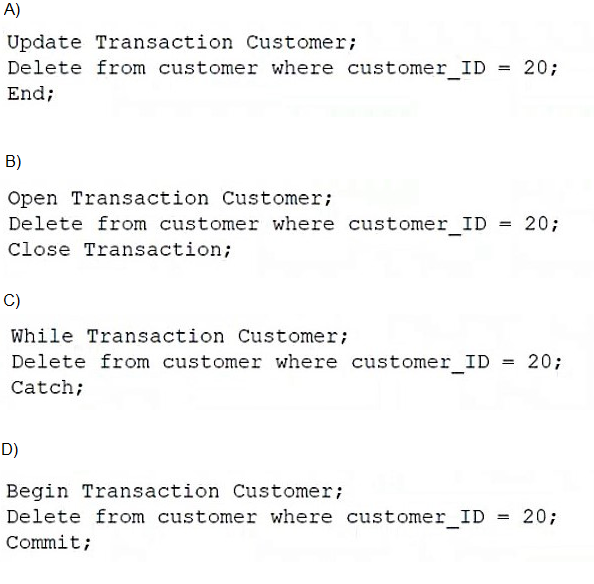
A. Option A
B. Option B
C. Option C
D. Option D
Explanation:
To safely and permanently remove data from a database, an administrator should use Transaction Control Language (TCL) commands to ensure the operation is executed as a single, atomic unit of work.
Why Option D is Correct
This option follows the standard logical flow for a managed database transaction:
Begin Transaction: This command explicitly starts the transaction block, signaling to the database that the following commands are part of a grouped operation.
Delete Statement: This is the Data Manipulation Language (DML) command used to remove specific rows based on a condition (in this case, customer_ID = 20).
Commit: This is the final and most crucial step. It tells the database to permanently save the changes made during the transaction. Without a COMMIT, the changes could be rolled back, and the data would not be permanently removed.
Why Other Options are Incorrect
Option A:
Uses Update Transaction and End. UPDATE is used to modify existing data, not to manage the lifecycle of a deletion block. End is also not a standard replacement for Commit in TCL.
Option B:
Uses Open Transaction and Close Transaction. These are not standard SQL keywords for controlling transactional integrity.
Option C:
Uses While and Catch. While is a procedural looping construct, and Catch is used for error handling. Neither is used to initiate or finalize a standard data deletion transaction.
References
CompTIA DataSys+ (DS0-001) Objective 1.3: "Explain the use of common SQL statements." This includes distinguishing between DML (DELETE) and TCL (BEGIN, COMMIT, ROLLBACK) commands.
A database administrator would like to create a table named XYZ. Which of the following
queries should the database administrator use to create the table?
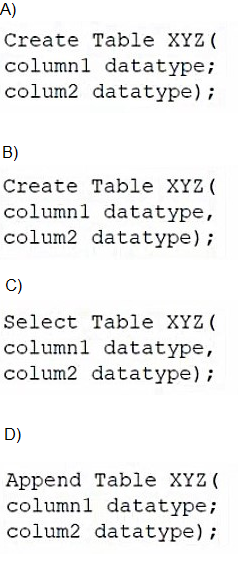
A. Option A
B. Option B
C. Option C
D. Option D
Explanation:
The correct query to create a table requires precise Data Definition Language (DDL) syntax. In standard SQL, the CREATE TABLE statement follows a specific structural pattern to define the object name, its columns, and their associated data types.
Why Option B is Correct
Option B adheres to the ANSI SQL standard for creating relational objects:
Statement Structure: It correctly uses the CREATE TABLE command followed by the identifier XYZ.
Column Separation: It uses a comma (,) to separate the definition of column1 and column2. This is a strict requirement for the database to parse the list of attributes correctly.
Encapsulation: All column definitions are properly enclosed within parentheses, signaling the beginning and end of the table's schema definition.
Why Other Options are Incorrect
Option A:
This option incorrectly uses a semicolon (;) to separate the columns. In SQL, a semicolon is a statement terminator used to end an entire command; using it inside the parentheses causes a syntax error because the database thinks the command ended prematurely.
Option C:
This uses the SELECT keyword. SELECT is a Data Query Language (DQL) command used to retrieve data from existing tables, not to define new storage structures.
Option D:
This uses the APPEND keyword. While some legacy systems or specific file-based databases use "Append," it is not a standard SQL command for object creation and would fail in a relational database management system (RDBMS).
References
CompTIA DataSys+ (DS0-001) Objective 1.3: "Explain the use of common SQL statements." Candidates must distinguish between DDL (creating/modifying objects) and DML (manipulating data).
Which of the following cloud delivery models provides users with thehighestlevel of flexibility regarding resource provisioning and administration?
A. DBaaS
B. IaaS
C. SaaS
D. PaaS
Explanation:
In the context of cloud delivery models, flexibility is determined by the "stack" layer at which the provider hands off control to the user. IaaS provides the most granular control over the underlying environment.
Why IaaS is Correct
Resource Provisioning: IaaS provides virtualized computing resources over the internet, such as virtual machines, storage, and networking.
Highest Flexibility: Because users are responsible for managing the operating system, middleware, and the database engine itself, they have the freedom to configure the environment to meet highly specific requirements.
Administrative Control: Unlike other models, the administrator has "root" or "system" level access to the server, allowing for custom configurations that are often locked down in managed services.
Why Other Options are Incorrect
A. DBaaS (Database as a Service):
This is a specialized form of PaaS. While it simplifies administration, it restricts flexibility because the provider manages the underlying OS and database tuning parameters.
C. SaaS (Software as a Service):
This offers the lowest level of flexibility. Users interact only with the software interface; they have no control over the infrastructure or the database engine.
D. PaaS (Platform as a Service):
PaaS provides a framework for developers to build applications without managing the underlying infrastructure. While it offers more flexibility than SaaS, it is more restrictive than IaaS because the platform's configuration is managed by the provider.
References
CompTIA DataSys+ (DS0-001) Objective 2.1: "Select an appropriate database deployment method." This includes understanding the trade-offs between IaaS, PaaS, and SaaS regarding maintenance, cost, and control.
Which of the following statements contains an error?
A. Select EmpId from employee where EmpId=90030
B. Select EmpId where EmpId=90030 and DeptId=34
C. Select* from employee where EmpId=90030
D. Select EmpId from employee
Explanation:
The error in this statement is a syntax error caused by the omission of a mandatory SQL clause required for data retrieval.
Why Option B Contains an Error
In structured query language, the SELECT statement must follow a specific logical order to execute correctly.
Why Other Options are Correct
A. Select EmpId from employee where EmpId=90030:
This is syntactically perfect. It defines the column, the table, and a specific filter.
C. Select from employee where EmpId=90030:* This is correct.
The asterisk (*) is a wildcard used to select all columns from the employee table for the specified ID.
D. Select EmpId from employee: This is correct.
A WHERE clause is optional; this query would simply return the EmpId for every row in the table.
References
CompTIA DataSys+ (DS0-001) Objective 1.3: "Explain the use of common SQL statements." This objective requires mastery of Data Query Language (DQL) and the ability to troubleshoot broken syntax in basic queries.
Which of the following is used to write SQL queries in various programming languages?
A. Indexing
B. Object-relational mapping
C. Excel
D. Normalization
Explanation:
Object-Relational Mapping (ORM) is a programming technique that allows developers to interact with a relational database using the object-oriented paradigm of their preferred programming language (such as Python, Java, or C#) instead of writing raw SQL.
Why Object-Relational Mapping is Correct
Abstraction Layer: ORM libraries (like Hibernate for Java, Entity Framework for .NET, or SQLAlchemy for Python) act as a bridge, automatically converting data between incompatible type systems—objects in code and tables in a database.
Programmatic Queries:It allows developers to write queries using the native syntax of their programming language, which the ORM then "translates" into the appropriate SQL dialect for the underlying database engine.
Security and Maintenance: ORMs help prevent SQL injection attacks by automatically parameterizing queries and making the codebase easier to maintain by keeping data logic within the application code.
Why Other Options are Incorrect
A. Indexing:
This is a database performance optimization technique used to speed up data retrieval. While it affects how queries run, it is not a tool used to write queries within programming languages.
C. Excel:
This is a spreadsheet application. While it can connect to databases via ODBC or Power Query, it is a standalone tool and not a method used for writing SQL within application programming.
D. Normalization:This is the process of organizing data in a database to reduce redundancy and improve data integrity (e.g., First Normal Form, Second Normal Form). It is a design principle for the data structure, not a tool for writing queries.
References
CompTIA DataSys+ (DS0-001) Objective 1.1: "Compare and contrast different database types and structures." This includes understanding how applications interface with databases and the role of ORMs in modern development.
Which of the following is a result of an on-path attack on a system?
A. A Wi-Fi networkthat redirects to clones of legitimate websites
B. A website that has crashed and is no longer accessible
C. An email from an unknown source requesting bank account details
D. A web application that returns the addresses of its customers
Explanation:
An on-path attack (formerly known as a Man-in-the-Middle or MITM attack) occurs when an attacker positions themselves between two communicating parties to intercept, monitor, or alter the data being exchanged.
Why Option A is Correct
Interception: In an on-path attack, the attacker often sets up a rogue access point or compromises a network to sit between the user and the internet.
Redirection: By controlling the path of the traffic, the attacker can intercept a request for a legitimate site (like a bank) and redirect the user to a clone (a malicious look-alike). This allows the attacker to steal credentials while the user believes they are on a secure connection.
Why Other Options are Incorrect
B. A website that has crashed:
This describes a Denial of Service (DoS) or Distributed Denial of Service (DDoS) attack, where the goal is to exhaust resources and make the service unavailable, rather than intercepting traffic.
C. An email requesting bank details:
This is an example of Phishing. While it is a social engineering attack used to steal data, it does not involve the attacker physically or logically sitting "on-path" between two active systems during a communication session.
D. A web application returning customer addresses:
This is typically the result of an Injection attack (like SQL Injection) or a broken access control vulnerability, where the database is forced to leak information it shouldn't, rather than the data being intercepted in transit.
References
CompTIA DataSys+ (DS0-001) Objective 4.1: "Summarize standard methods to secure data." This objective covers various threat actors and attack vectors, including on-path attacks, and the importance of encryption (like TLS) in preventing them.
Which of the following ismostlikely to prevent tampering with server hardware that houses data?
A. Biometric locks
B. Strong password policy
C. Network firewall
D. Surveillance cameras
Explanation:
When the goal is to prevent physical tampering with server hardware, administrators must implement physical security controls that restrict access to the hardware itself.
Why Other Options are Incorrect
B. Strong password policy:
This is a logical security control. While it prevents unauthorized login to the operating system or database, it does not stop someone from physically removing a hard drive or resetting hardware components.
C. Network firewall:
A firewall is a technical control designed to filter network traffic. It protects against remote attacks but offers no defense against an individual standing in the same room as the server.
D. Surveillance cameras:
Cameras are a detective control. While they provide a record of who tampered with the hardware and may act as a deterrent, they do not physically prevent the act from occurring in the moment.
References
CompTIA DataSys+ (DS0-001) Objective 4.2: "Given a scenario, configure database access controls." This includes the implementation of physical security measures to protect the integrity of the data environment.
A database's daily backup failed. Previous backups were completed successfully. Which of the following should the database administrator examinefirstto troubleshoot the issue?
A. CPU usage
B. Disk space
C. Event log
D. OS performance
Explanation:
When a specific task like a database backup fails after a period of success, the most efficient troubleshooting step is to identify the specific error message generated by the system.
Why Other Options are Incorrect
A. CPU usage:
High CPU usage can slow down a backup, but it rarely causes a total failure unless the system crashes entirely. It is a secondary performance metric, not a primary diagnostic for a task failure.
B. Disk space:
While insufficient disk space is a common cause of backup failure, checking it first is a "guess." The Event log would confirm if disk space was indeed the reason for the failure before the administrator spends time clearing files.
D. OS performance:
General OS performance is too broad of a metric. Like CPU usage, it monitors the "health" of the system rather than the "outcome" of a specific database operation.
References
CompTIA DataSys+ (DS0-001) Objective 3.3: "Given a scenario, monitor and optimize database performance." This includes using logs and monitoring tools to diagnose specific failures.
| Page 2 out of 12 Pages |
