Free CompTIA CAS-005 Practice Questions 2026 - Page 12
An organization recently implemented a new email DLP solution. Emails sent from company email addresses to matching personal email addresses generated a large number of alerts, but the content of the emails did not include company data. The security team needs to reduce the number of emails sent without blocking all emails to common personal email services. Which of the following should the security team implement first?
A. Automatically quarantine outgoing email.
B. Create an acceptable use policy.
C. Enforce email encryption standards.
D. Perform security awareness training focusing on phishing.
Explanation:
The alerts show employees frequently emailing personal addresses, but the content contains no company data. This suggests a policy gap rather than a technical control failure. Before implementing technical blocks or restrictions, the organization should establish or reinforce an acceptable use policy (AUP) that defines proper use of corporate email, including when and why personal email addresses can be used.
Correct Option:
B. Create an acceptable use policy.
An AUP sets clear expectations about using corporate email to contact personal external addresses.
It provides the governance basis for any subsequent technical controls (e.g., blocking, quarantining).
Many alerts may be legitimate (e.g., sending a meeting confirmation to a personal calendar).
Without an AUP, the security team lacks authority to restrict behavior. Policy should come before technology.
Incorrect Options:
A. Automatically quarantine outgoing email.
Quarantining adds operational overhead and may disrupt legitimate communications.
Alerts show no company data leakage, so quarantine is an overreaction.
Technical control without policy is likely to be bypassed or cause user frustration. This is premature.
C. Enforce email encryption standards.
Encryption protects confidentiality, but the issue is volume of alerts, not data exposure.
Emails without company data do not need encryption.
This does not reduce alert volume or address the root cause (lack of policy guidance).
D. Perform security awareness training focusing on phishing.
Phishing training addresses malicious incoming emails or credential theft, not outgoing emails to personal addresses.
The users are not acting maliciously or falling for phishing; they are using corporate email to contact personal accounts.
Training is useful but does not solve the alert volume problem as a first step.
Reference:
CompTIA CAS-005 Exam Objectives — Domain 4: Governance, Risk, and Compliance (Policy Development). NIST SP 800-53 (PL-2: System Security and Privacy Plan — includes AUP). SANS Policy Framework — "An acceptable use policy should be established before implementing restrictive technical controls on email."
A company designs policies and procedures for hardening containers deployed in the production environment. However, a security assessment reveals that deployed containers are not complying with the security baseline. Which of the following solutions best addresses this issue throughout early life-cycle stages?
A. Installing endpoint agents on each container and setting them to report when configurations drift from the baseline
B. Finding hardened container images and enforcing them as the baseline for new deployments
C. Creating a pipeline to check the containers through security gates and validating the baseline controls before the final deployment
D. Running security assessments regularly and checking for the security baseline on containers already in production
Explanation:
The issue is that deployed containers do not comply with the security baseline. The question asks for a solution that addresses this throughout early life‑cycle stages (build, CI/CD, pre‑deployment). Shifting security left — integrating validation gates in the pipeline — ensures containers are checked and hardened before reaching production, preventing non‑compliant deployments.
Correct Option:
C. Creating a pipeline to check the containers through security gates and validating the baseline controls before the final deployment
Integrates security scans (e.g., CIS benchmark checks, vulnerability scans) into the CI/CD pipeline.
Prevents non‑compliant containers from being deployed by failing the build or blocking promotion.
Addresses the root cause — non‑compliance at deployment time — rather than detecting drift after deployment.
This is a shift‑left, automated solution suitable for early life‑cycle stages.
Incorrect Options:
A. Installing endpoint agents on each container and setting them to report when configurations drift from the baseline
Agents inside containers add overhead and complexity; containers are meant to be ephemeral and immutable.
This detects drift after deployment (reactive), not preventing non‑compliance early in the life cycle.
Does not address the root cause of deploying non‑compliant containers.
B. Finding hardened container images and enforcing them as the baseline for new deployments
Hardened base images are good, but without pipeline validation, developers can still add layers or modify configurations that break compliance.
“Enforcing” at deployment time without pre‑deployment gates is insufficient.
Misses the early‑stage checking requirement.
D. Running security assessments regularly and checking for the security baseline on containers already in production
This is purely reactive — detecting issues after containers are already running.
Does not prevent non‑compliant containers from being deployed.
Violates the “early life‑cycle stages” requirement.
Reference:
CompTIA CAS-005 Exam Objectives — Domain 2: Security Operations (DevSecOps, Container Security, Shift Left). NIST SP 800‑190 (Application Container Security Guide) — “Security gates in the CI/CD pipeline are recommended to enforce container hardening prior to production.” OWASP CI/CD Security Cheat Sheet.
A company must meet the following security requirements when implementing controls in
order to be compliant with government policy:
• Access to the system document repository must be MFA enabled.
• Ongoing risk monitoring must be displayed on a system dashboard.
• Staff must receive email notifications about periodic tasks.
Which of the following best meets all of these requirements?
A. Implementing a GRC tool
B. Configuring a privileged access management system
C. Launching a vulnerability management program
D. Creating a risk register
Explanation:
The three requirements are: MFA for a document repository, an ongoing risk monitoring dashboard, and email notifications for periodic tasks. A Governance, Risk, and Compliance (GRC) tool centralizes policy management, risk tracking, and automated notifications. It can integrate with identity systems for MFA enforcement and provide dashboards, meeting all three requirements in one solution.
Correct Option:
A. Implementing a GRC tool
GRC tools (e.g., RSA Archer, ServiceNow GRC) provide risk dashboards for ongoing monitoring.
They support automated email notifications for compliance tasks, audits, and policy reviews.
They can integrate with identity providers (e.g., SAML, LDAP) to enforce MFA on connected repositories.
This single solution addresses all three required controls.
Incorrect Options:
B. Configuring a privileged access management system
PAM focuses on securing administrative accounts, session recording, and password vaulting.
It does not provide a risk dashboard or email notifications for periodic compliance tasks.
MFA for document access may be partially supported, but the other requirements are unmet.
C. Launching a vulnerability management program
Vulnerability management scans for technical weaknesses (CVEs, misconfigurations).
It does not enforce MFA on document repositories nor send task notifications.
Risk dashboards in VM tools show only technical vulnerabilities, not ongoing compliance risk.
D. Creating a risk register
A risk register is a static document or spreadsheet listing identified risks.
It does not enforce MFA, does not provide an automated dashboard, and does not send notifications.
This is a manual artifact, not an automated control solution.
Reference:
CompTIA CAS-005 Exam Objectives — Domain 4: Governance, Risk, and Compliance (GRC Tools, Policy Enforcement). NIST SP 800-53 (CA-7: Continuous Monitoring — GRC tools support dashboards). ISO 31000 (Risk management — GRC platforms automate monitoring).
A systems engineer is configuring SSO for a business that will be using SaaS applications for its remote-only workforce. Privileged actions in SaaS applications must be allowed only from corporate mobile devices that meet minimum security requirements, but BYOD must also be permitted for other activity. Which of the following would best meet this objective?
A. Block any connections from outside the business's network security boundary.
B. Install machine certificates on corporate devices and perform checks against the clients.
C. Configure device attestations and continuous authorization controls.
D. Deploy application protection policies using a corporate, cloud-based MDM solution.
Explanation:
The requirement distinguishes between privileged actions (allowed only from compliant corporate mobile devices) and non‑privileged activity (allowed from BYOD). Device attestation verifies security posture (e.g., encryption, OS version, jailbreak status) at access time. Continuous authorization re‑evaluates trust during a session, ensuring privileged actions remain restricted to compliant devices even after initial authentication.
Correct Option:
C. Configure device attestations and continuous authorization controls.
Device attestation (e.g., via mobile device compliance checks) confirms that corporate devices meet minimum security requirements.
Continuous authorization allows privileged actions only while the device remains in a compliant state.
BYOD can still access non‑privileged features without attestation.
This aligns with zero trust principles and least privilege without blocking BYOD entirely.
Incorrect Options:
A. Block any connections from outside the business's network security boundary.
Remote‑only workforce has no “inside” network boundary; this would block all remote access.
BYOD and corporate devices would both be blocked.
Does not differentiate between privileged vs. non‑privileged actions.
B. Install machine certificates on corporate devices and perform checks against the clients.
Certificate‑based authentication verifies device identity but not security posture (e.g., patched OS, encryption enabled).
Does not ensure devices meet minimum security requirements.
Certificates alone cannot enforce continuous authorization or differentiate action types.
D. Deploy application protection policies using a corporate, cloud-based MDM solution.
MDM can enforce policies on enrolled corporate devices but typically requires full device management.
May not support granular per‑action authorization (privileged vs. non‑privileged) within a single SaaS app.
BYOD would either need enrollment (defeating BYOD purpose) or be blocked entirely.
Device attestation is more flexible and privacy‑preserving for BYOD scenarios.
Reference:
CompTIA CAS-005 Exam Objectives — Domain 1: Security Architecture (Zero Trust, Conditional Access). NIST SP 800-207 (Zero Trust Architecture) — Device attestation and continuous authorization are core components. Google BeyondCorp model — “Trust is determined continuously based on device posture, not just network location.”
An attacker infiltrated the code base of a hardware manufacturer and inserted malware before the code was compiled. The malicious code is now running at the hardware level across a number of industries and sectors. Which of the following categories best describes this type of vendor risk?
A. SDLC attack
B. Side-load attack
C. Remote code signing
D. Supply chain attack
Explanation:
The attacker compromised the hardware manufacturer's code base before compilation, and the resulting malicious code is now distributed downstream across multiple industries. This is a classic supply chain attack — compromising a trusted vendor (hardware manufacturer) to inject malware into products that customers then deploy, affecting the entire downstream ecosystem.
Correct Option:
D. Supply chain attack
The hardware manufacturer is a supplier in the customers' supply chain.
Malware inserted at the source (code base) propagates to all customers who use the manufactured components.
This affects multiple industries and sectors, demonstrating supply chain risk.
Examples include SolarWinds, NotPetya (via M.E.Doc), and hardware-level implants (e.g., Supermicro).
Incorrect Options:
A. SDLC attack
While the attack occurred during the software development life cycle (specifically in the code base), this term is too narrow.
The key risk is not just where it happened, but the vendor‑customer relationship that spread the malware.
"SDLC attack" does not capture the downstream impact across organizations.
B. Side-load attack
Side-loading refers to installing an application using an unofficial or unsigned package, bypassing official stores (e.g., sideloading APKs on Android).
This scenario involves code injection at the manufacturer, not end‑user installation from an unofficial source.
Not applicable.
C. Remote code signing
Code signing (remote or local) is a technique to verify software authenticity and integrity.
The scenario describes malware injection before compilation; signing may still occur, but that is not the risk category.
Remote code signing would not have prevented or caused the described compromise.
Reference:
CompTIA CAS-005 Exam Objectives — Domain 4: Governance, Risk, and Compliance (Supply Chain Risk Management). NIST SP 800-161 (Supply Chain Risk Management Practices). Executive Order 14028 (Improving the Nation's Cybersecurity) — “Supply chain attacks compromise vendors to reach downstream customers.”
A social media company wants to change encryption ciphers after identifying weaknesses
in the implementation of the existing ciphers. The company needs the new ciphers to meet
the following requirements:
• Be more CPU-efficient than previous ciphers.
• Require customers to use TLS 1.3 while broadcasting video or audio.
Which of the following is the best choice for the social media company?
A. IDEA-CBC
B. AES-GCM
C. ChaCha20-Poly1305
D. Camellia-CBC
Explanation:
ChaCha20-Poly1305 is a stream cipher (with an authenticator) designed for high performance on devices with limited hardware acceleration. It uses less RAM, is CPU‑efficient (especially on ARM or older x86 without AES‑NI), and is explicitly supported in TLS 1.3 as a mandatory‑to‑implement cipher suite. These properties match all three requirements.
Correct Option:
C. ChaCha20‑Poly1305
Less RAM: Stream cipher maintains minimal state; authenticated encryption with Poly1305 has low memory footprint.
CPU‑efficient: Excellent performance on software‑only implementations; avoids AES‑NI dependency.
TLS 1.3: Defined in RFC 8446 and RFC 7905 for TLS 1.3 and DTLS. Used by Chrome, Cloudflare, Google for video/audio streaming.
Designed for mobile/embedded systems, making it ideal for customer devices broadcasting media.
Incorrect Options:
A. IDEA‑CBC
IDEA is an old block cipher (64‑bit block) and is not approved for TLS 1.3.
CBC mode is deprecated in TLS 1.3.
Not CPU‑efficient compared to modern ciphers; higher memory usage.
Does not meet TLS 1.3 requirement.
B. AES‑GCM
AES‑GCM is excellent and TLS 1.3 compliant, but it consumes more RAM (galois tables) and requires AES‑NI for efficient CPU use.
On devices without AES‑NI (older or low‑power CPUs), it is less CPU‑efficient than ChaCha20.
Requirement says “more CPU‑efficient than previous ciphers” — if previous ciphers were also AES‑based, this may not hold. ChaCha20 is explicitly optimized for software.
D. Camellia‑CBC
Camellia is a secure block cipher but uses CBC mode, which is not permitted in TLS 1.3.
CBC mode is vulnerable to padding oracle attacks and was removed from TLS 1.3.
Not validated for the stated use case (TLS 1.3 media broadcast).
Reference:
CompTIA CAS-005 Exam Objectives — Domain 1: Security Architecture (Cryptography, TLS 1.3, Cipher Suites).
RFC 8446 (TLS 1.3) — Section 9.1 lists ChaCha20‑Poly1305 as a valid authenticated encryption with associated data (AEAD) algorithm.
RFC 7905 (ChaCha20‑Poly1305 Cipher Suites for TLS).
Cloudflare blog: “ChaCha20‑Poly1305 is faster than AES‑GCM on mobile devices without hardware acceleration.”
A malware researcher has discovered a credential stealer is looking at a specific memory register to harvest passwords that will be used later for lateral movement in corporate networks. The malware is using TCP 4444 to communicate with other workstations. The lateral movement would be best mitigated by:
A. Configuring the CPU's NX bit
B. Enabling a host firewall
C. Enabling an edge firewall
D. Enforcing all systems to use UEFI
E. Enabling ASLR on the Active Directory server
Explanation:
The malware uses TCP port 4444 for lateral movement between workstations inside the corporate network. An edge firewall protects the perimeter but does not block east‑west traffic between internal workstations. A host‑based firewall on each workstation can block inbound/outbound connections on port 4444, directly preventing the malware from communicating laterally.
Correct Option:
B. Enabling a host firewall
Host firewall (e.g., Windows Defender Firewall, iptables) controls traffic to and from each individual workstation.
Can be configured to block TCP 4444 (or any port) regardless of source or destination IP.
Effective against east‑west lateral movement even if workstations are on the same subnet.
Does not require network infrastructure changes.
Complements perimeter controls by enforcing micro‑segmentation at the endpoint.
Incorrect Options:
A. Configuring the CPU's NX bit
NX (No‑eXecute) bit prevents code execution from memory regions marked as non‑executable (buffer overflow mitigation).
Credential stealers harvesting memory registers are not necessarily executing shellcode; NX does not block network communication.
Does not mitigate TCP 4444 lateral movement.
C. Enabling an edge firewall
Edge firewalls protect the boundary between internal and external networks.
Lateral movement occurs inside the network, so edge firewall rules have no effect.
Traffic between two workstations may never traverse the edge firewall.
D. Enforcing all systems to use UEFI
UEFI (replacing BIOS) provides boot‑time security features like Secure Boot.
Protects against bootkits and rootkits, not credential stealers or network communication.
Unrelated to blocking TCP 4444 lateral movement.
E. Enabling ASLR on the Active Directory server
ASLR (Address Space Layout Randomization) randomizes memory addresses to make exploitation harder.
Useful against memory corruption attacks, but this malware harvests credentials from a specific register (likely via legitimate access or already running code).
Does not block network communication on port 4444.
ASLR is typically already enabled on modern OS; enabling it on a specific server does not stop workstation‑to‑workstation communication.
Reference:
CompTIA CAS-005 Exam Objectives — Domain 2: Security Operations (Endpoint Security, Host‑Based Firewalls, Lateral Movement Mitigation). NIST SP 800-207 (Zero Trust Architecture) — “Host‑based firewalls are a key control for east‑west segmentation.” MITRE ATT&CK ID TA0008 (Lateral Movement) — mitigation: “Block unnecessary ports using host firewall.”
A company's Chief Information Security Officer learns that the senior leadership team is traveling to a country accused of attempting to steal intellectual property saved on laptops. Which of the following is the best method to protect against this attack?
A. Configure Measured Boot to report any firmware changes.
B. Use sanitized devices with remote connections to VDI.
C. Deploy self-encrypting drives to protect company data.
D. Install tamper-evident stickers over any laptop screws.
Explanation:
The threat is physical access to laptops in a hostile country where intellectual property theft is likely. Traditional encryption (self-encrypting drives) protects data at rest but does not prevent keyloggers, cold‑boot attacks, or bypasses while the device is unlocked. Using sanitized devices with remote connections to a Virtual Desktop Infrastructure (VDI) ensures no sensitive data ever resides on the local laptop.
Correct Option:
B. Use sanitized devices with remote connections to VDI.
Sanitized devices contain no sensitive data locally (clean OS, no stored IP).
VDI keeps all data and applications in the corporate data center or cloud.
If the device is seized or compromised, only the thin client is lost, not the intellectual property.
Remote connections can be further secured with MFA and session timeouts.
This is the best protection against physical access threats in high‑risk locations.
Incorrect Options:
A. Configure Measured Boot to report any firmware changes.
Measured Boot detects and reports unauthorized firmware/bootloader changes.
It does not prevent data theft from an unlocked or running laptop.
Useful for integrity attestation, but the attacker can simply copy files while the device is in use.
Does not protect IP once the user authenticates.
C. Deploy self-encrypting drives to protect company data.
SEDs encrypt data at rest, protecting against offline theft of a powered‑off laptop.
When the laptop is powered on and unlocked (during travel, daily use), the drive is decrypted and data is accessible.
Attackers can steal data while the system is running (USB copy, screen capture, keylogging).
Insufficient for this scenario.
D. Install tamper-evident stickers over any laptop screws.
Stickers show physical tampering but do not prevent data access.
An attacker can bypass screws via other means (e.g., booting from USB, removing SSD if accessible).
Does not protect intellectual property on an unlocked device.
Reactive indicator, not a protective control.
Reference:
CompTIA CAS-005 Exam Objectives — Domain 2: Security Operations (Mobile Device Security, VDI, Travel Security). NIST SP 800-114 (User’s Guide to Telework and Bring Your Own Device) — “Use VDI for high‑risk travel to avoid storing data locally.” NSA Travel Security Guidance — sanitized devices with no persistent data are recommended for high‑threat destinations.
After a cybersecurity incident, a security analyst was able to collect a binary that the
attacker used on the compromised server. Then the analyst ran the following command:
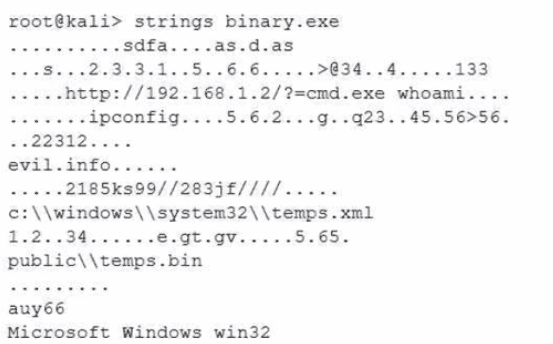
Which of the following options describes what the analyst is trying to do?
A. To reconstruct the timeline of commands executed by the binary
B. To extract loCs from the binary used on the attack
C. To replicate the attack in a secure environment
Explanation:
The command shown is strings binary.exe, which extracts human‑readable strings from a binary file. The output includes IP addresses (192.168.1.2), domain names (evil.info), Windows commands (whoami, ipconfig), file paths (c:\windows\system32\temps.xml), and other artifacts. The analyst is clearly extracting Indicators of Compromise (IoCs) from the attacker’s binary.
Correct Option:
B. To extract IoCs from the binary used on the attack
The strings command is a standard tool for extracting printable character sequences from binary files.
Output reveals IPs, domains, file paths, and executed commands — all valuable IoCs.
These IoCs can be used to hunt for other compromised systems, write detection rules, or block malicious infrastructure.
No replication or timeline reconstruction is performed by strings.
Incorrect Options:
A. To reconstruct the timeline of commands executed by the binary
strings does not provide temporal sequencing or execution order.
It simply extracts static strings embedded in the binary, not a log of runtime execution.
Timeline reconstruction would require dynamic analysis (e.g., running the binary in a sandbox with process monitoring).
C. To replicate the attack in a secure environment
strings is a passive, static analysis tool; it does not execute or replicate the binary.
Replication requires executing the binary in a sandbox or debugger (dynamic analysis).
Running strings does not create a secure copy of the attack environment.
Reference:
CompTIA CAS-005 Exam Objectives — Domain 3: Security Operations (Malware Analysis, Indicator Extraction). MITRE ATT&CK — “Strings extraction is a static analysis technique used to identify IoCs such as IP addresses, domains, and file paths.” SANS FOR610 (Reverse‑Engineering Malware) — strings is a first‑step tool for IoC harvesting.
A company that uses several cloud applications wants to properly identify: All the devices potentially affected by a given vulnerability. All the internal servers utilizing the same physical switch. The number of endpoints using a particular operating system.Which of the following is the best way to meet the requirements?
A. SBoM
B. CASB
C. GRC
D. CMDB
Explanation:
The company uses several cloud applications and needs asset visibility (vulnerable devices, OS counts, and physical switch mapping). A CASB (Cloud Access Security Broker) discovers all devices accessing cloud apps, tracks OS versions, and can integrate with on‑premises asset tools or APIs to map network topology, including physical switch relationships, through agent or agentless connectors.
Correct Option:
B. CASB
Discovers all managed and unmanaged devices (including BYOD) accessing cloud applications.
Can identify OS versions across endpoints from cloud app logs or MDM integration.
Some CASBs integrate with network discovery tools or CMDBs to map device‑to‑switch relationships.
Provides vulnerability correlation by linking CVEs to devices detected via cloud access.
Centralizes visibility across multi‑cloud and hybrid environments.
Incorrect Options:
A. SBoM (Software Bill of Materials)
Lists software components and dependencies within an application, not devices or network topology.
Does not identify servers on a physical switch or count endpoints by OS.
Too narrow in scope; focused on software supply chain, not asset inventory.
C. GRC (Governance, Risk, and Compliance)
Manages policies, risk assessments, and compliance evidence.
Does not actively discover devices, map network switches, or enumerate OS versions.
Relies on other tools (e.g., CASB, CMDB) for asset data inputs.
D. CMDB (Configuration Management Database)
Excellent for on‑premises asset inventory and relationships (e.g., server‑to‑switch mapping).
However, the question emphasizes cloud applications, where CASB provides native discovery of cloud‑connected devices.
CMDBs often lack real‑time visibility into shadow IT and cloud‑only devices without integration.
CASB is the better first choice given the “several cloud applications” context.
Reference:
CompTIA CAS-005 Exam Objectives — Domain 3: Security Operations (Cloud Security, CASB). NIST SP 800‑210 (General Access Control Guidance for Cloud Systems) — CASB provides asset discovery across cloud apps. Gartner definition of CASB: “Visibility into devices accessing cloud services, including OS enumeration and vulnerability correlation.”
| Page 12 out of 36 Pages |
