Free CompTIA CAS-005 Practice Questions 2026 - Page 11
A compliance officer isfacilitating abusiness impact analysis (BIA)and wantsbusiness unit leadersto collect meaningful data. Several business unit leaders want more information about the types of data the officer needs. Which of the following data types would be the most beneficial for the compliance officer?(Select two)
A. Inventory details
B. Applicable contract obligations
C. Costs associated with downtime
D. Network diagrams
E. Contingency plans
F. Critical processes
C. Costs associated with downtime
F. Critical processes
Explanation:
A Business Impact Analysis (BIA) identifies critical functions and quantifies the impact of disruption. For a compliance officer, the most beneficial data are costs of downtime (to calculate recovery priorities) and critical processes (to map regulatory and operational dependencies). Contract obligations support this but are secondary.
Correct Options (best two):
C. Costs associated with downtime
Directly measures financial, operational, and regulatory impact per outage duration.
Enables calculation of Recovery Time Objectives (RTO) and Recovery Point Objectives (RPO).
Essential for compliance with BIA requirements in standards like ISO 22301 and FFIEC.
F. Critical processes
Identifies which business functions are time-sensitive and legally/compliance-critical.
Helps map dependencies (people, technology, third parties) for continuity planning.
Directly feeds into compliance with regulations requiring process-level risk assessment (e.g., GLBA, HIPRA, DORA).
B. Applicable contract obligations
Important for legal and financial risk, but in a BIA it supports downtime cost calculations rather than being a primary data type.
Without knowing critical processes and downtime costs, contract obligations lack prioritization context.
Still useful, but secondary to C and F.
Incorrect Options (not selected):
A. Inventory details
Lists assets (hardware, software) but does not reveal business impact or compliance risk.
BIA focuses on processes and financial loss, not asset counts. More relevant to asset management or CMDB.
D. Network diagrams
Technical documentation for IT recovery, not business-unit impact data.
Compliance officer needs business outcomes, not network topology.
E. Contingency plans
These are outputs of BIA and continuity planning, not inputs.
BIA is conducted before developing contingency plans to inform their design.
Reference:
CompTIA CAS-005 Exam Objectives — Domain 4: Governance, Risk, and Compliance (Business Impact Analysis).
An administrator reviews the following log and determines the root cause of a site-to-site
tunnel failure:
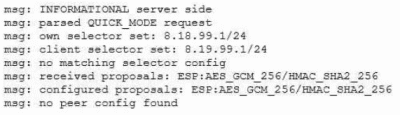
Which of the following actions should the administrator take to most effectively correct the
failure?
A. Enable perfect forward secrecy on the remote peer.
B. Update the cipher suites configured for use on the server side.
C. Add a new subnet as a permitted initiator.
D. Disable IKE version 1 and run IKE version 2.
Explanation:
The log indicates the tunnel fails because the server‑side has configured selector 8.18.99.1/24 but the client peer proposes 8.19.99.1/24. The error no matching selector config and no peer config found means the remote subnet is not allowed. The administrator must add the client’s subnet as a permitted initiator so that IPsec selectors match.
Correct Option:
C. Add a new subnet as a permitted initiator
The log shows client selector set: 8.19.99.1/24 and own selector set: 8.18.99.1/24.
The server has no matching selector configuration for the client’s subnet.
Adding 8.19.99.1/24 to the allowed initiator/protected subnets resolves the mismatch.
This is a common IPsec tunnel issue when local and remote traffic selectors do not align.
Incorrect Options:
A. Enable perfect forward secrecy on the remote peer
PFS affects key derivation (Diffie‑Hellman rekeying), not traffic selectors.
The failure is about subnet mismatch, not cryptographic key freshness. Enabling PFS will not resolve selector misalignment.
B. Update the cipher suites configured for use on the server side
The log shows proposals match: ESP:AES_GCM_256/HMAC_SHA2_256 is listed as both received and configured.
Cipher suite mismatch would cause a different error (e.g., no acceptable proposal). The actual error is selector‑related.
D. Disable IKE version 1 and run IKE version 2
The log shows QUICK_MODE, which is IKEv1 terminology. Switching to IKEv2 changes negotiation but does not fix mismatched subnets.
IKEv2 uses Child SAs, but the root cause (client subnet not permitted) remains unchanged.
Reference:
CompTIA CAS-005 Exam Objectives — Domain 2: Security Operations (Troubleshooting IPsec VPNs).
RFC 7296 (IKEv2) — Section 2.9 (Traffic Selectors).
StrongSwan/libreswan logs: “no matching selector config” indicates TS (traffic selector) mismatch.
A security engineer needs to review the configurations of several devices on the network to
meet the following requirements:
• The PostgreSQL server must only allow connectivity in the 10.1.2.0/24
subnet.
• The SSH daemon on the database server must be configured to listen
to port 4022.
• The SSH daemon must only accept connections from a Single
workstation.
• All host-based firewalls must be disabled on all workstations.
• All devices must have the latest updates from within the past eight
days.
•All HDDs must be configured to secure data at rest.
• Cleartext services are not allowed.
• All devices must be hardened when possible.
Instructions:
Click on the various workstations and network devices to review the posture assessment
results. Remediate any possible issues or indicate that no issue is found.
Click on Server A to review output data. Select commands in the appropriate tab to
remediate connectivity problems to the pOSTGREsql DATABASE VIA ssh
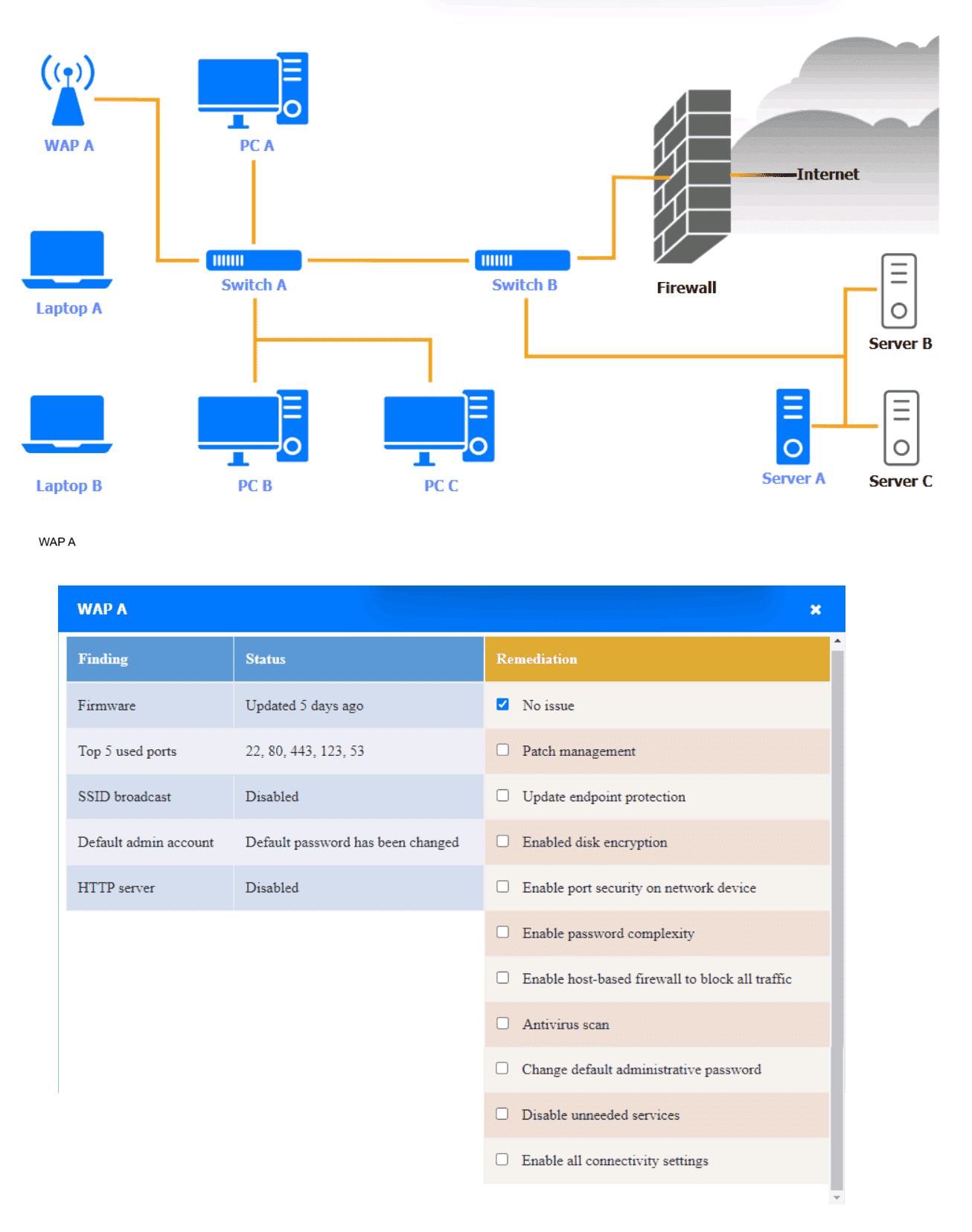
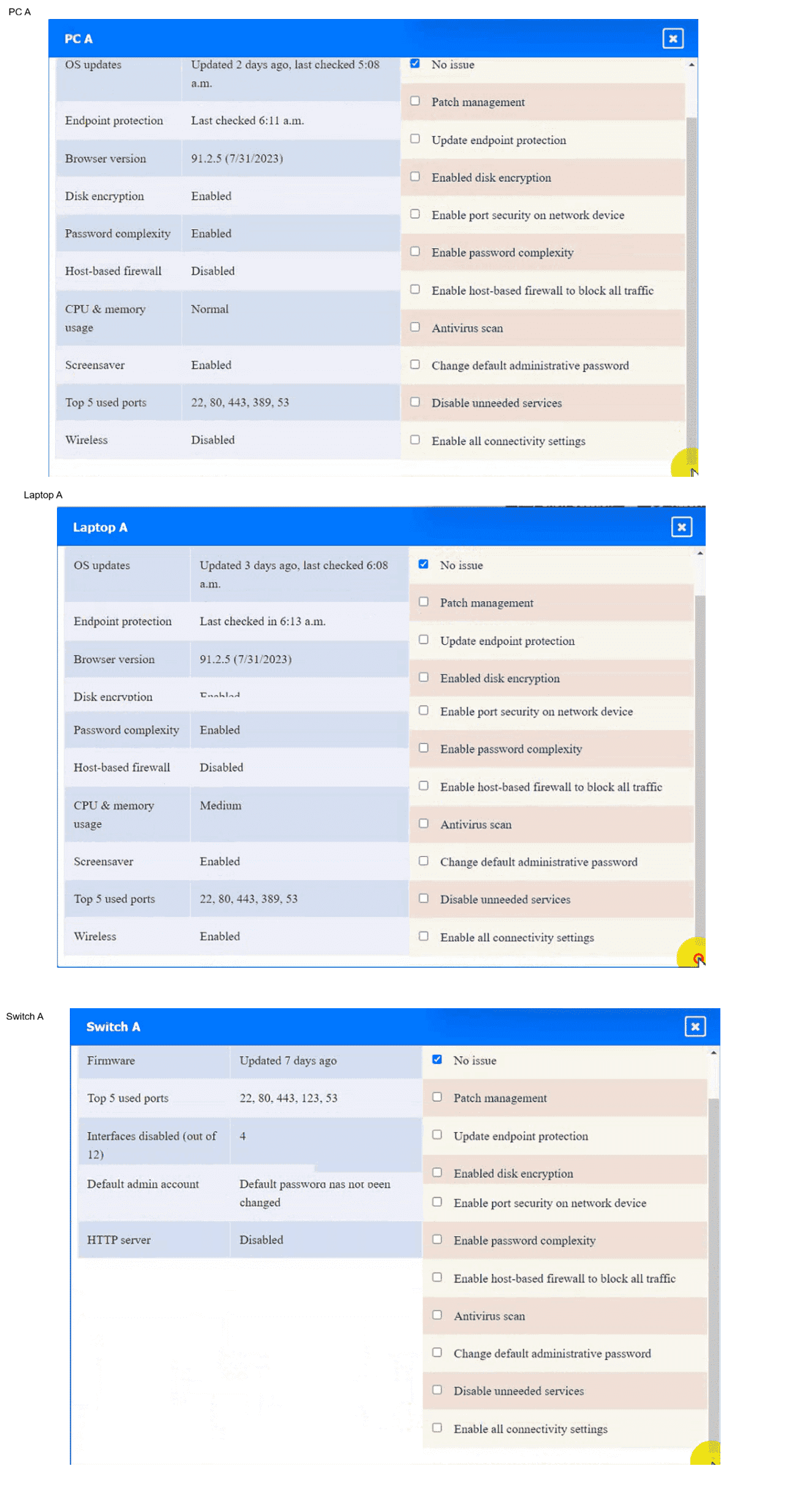
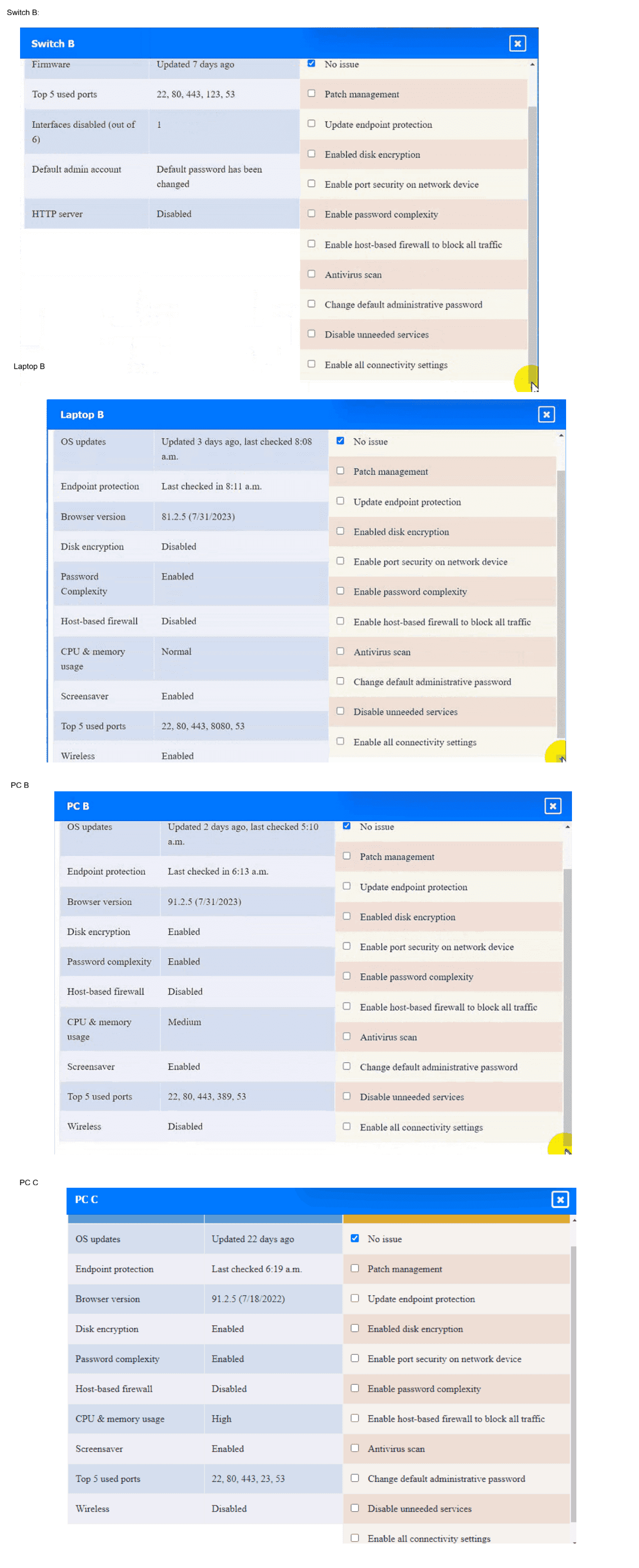

See the Explanation below for the solution.
A security professional is investigating a trend in vulnerability findings for newly deployed
cloud systems Given the following output:
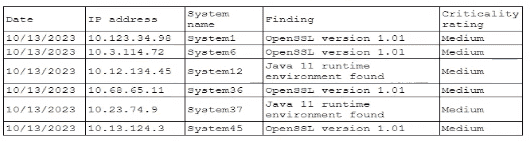
Which of the following actions would address the root cause of this issue?
A. Automating the patching system to update base Images
B. Recompiling the affected programs with the most current patches
C. Disabling unused/unneeded ports on all servers
D. Deploying a WAF with virtual patching upstream of the affected systems
Explanation:
The vulnerability trend shows outdated OpenSSL (version 1.01) and Java 11 runtime appearing repeatedly across multiple newly deployed cloud systems. This indicates the base images used for deployment contain outdated software versions. Fixing individual systems after deployment is reactive; the root cause is the image itself.
Correct Option:
A. Automating the patching system to update base images
The same outdated OpenSSL and Java versions appear on multiple systems (System1, System6, System36, System37, System45).
This pattern strongly suggests a golden image or infrastructure-as-code template with stale packages.
Updating the base image and automating its patching ensures all new deployments are secure from the start.
This addresses the root cause (image provenance) rather than treating symptoms.
Incorrect Options:
B. Recompiling the affected programs with the most current patches
Recompiling individual programs is time‑consuming and does not fix the underlying base image.
New deployments will still use the old image and re‑introduce the same vulnerabilities.
This is a reactive, per‑system fix, not a root‑cause solution for cloud deployments.
C. Disabling unused/unneeded ports on all servers
Port disabling reduces attack surface but does not patch outdated OpenSSL or Java libraries.
Vulnerabilities in OpenSSL can be exploited over any port where the service listens.
This is a compensating control, not a fix for outdated software versions.
D. Deploying a WAF with virtual patching upstream of the affected systems
Virtual patching blocks known exploits but does not remove the underlying vulnerable library.
It adds operational overhead and may miss zero‑days or variations of attacks.
Like port disabling, it is a temporary mitigation, not a root‑cause resolution.
Reference:
CompTIA CAS-005 Exam Objectives — Domain 2: Security Operations (Cloud Security & Automation). NIST SP 800‑190 (Application Container Security Guide) — recommends patching base images. AWS Well‑Architected Framework — Security Pillar: “Use updated AMIs.” CIS Benchmark for Cloud Computing — “Maintain hardened and updated golden images.”
During a recent audit, a company's systems were assessed- Given the following
information:
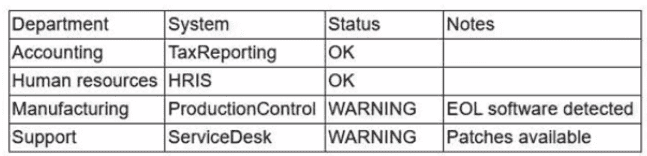
Which of the following is the best way to reduce the attack surface?
A. Deploying an EDR solution to all impacted machines in manufacturing
B. Segmenting the manufacturing network with a firewall and placing the rules in monitor mode
C. Setting up an IDS inline to monitor and detect any threats to the software
D. Implementing an application-aware firewall and writing strict rules for the application access
Explanation:
The audit shows Manufacturing has end-of-life (EOL) software and Support has missing patches. Reducing attack surface means limiting how attackers can interact with vulnerable systems. An application-aware firewall with strict rules restricts allowed traffic to only what is necessary for each application, directly minimizing exposure of EOL or unpatched software.
Correct Option:
D. Implementing an application-aware firewall and writing strict rules for the application access
EOL software cannot be patched, so compensating controls must reduce attack surface.
Application-aware firewalls (e.g., next-gen firewalls) filter based on application protocol, not just ports.
Strict rules allow only legitimate application traffic, blocking exploit attempts against vulnerable services.
This directly reduces exposure without requiring software replacement or network redesign.
Incorrect Options:
A. Deploying an EDR solution to all impacted machines in manufacturing
EDR detects and responds to threats but does not reduce attack surface; it adds detection capability.
EOL software remains vulnerable, and EDR can be bypassed. Attack surface (open ports, running services) stays the same.
B. Segmenting the manufacturing network with a firewall and placing the rules in monitor mode
Monitor mode only observes traffic; it does not enforce segmentation or block malicious access.
Without active blocking, attack surface is unchanged. Segmentation helps only when rules are enforced (block mode).
C. Setting up an IDS inline to monitor and detect any threats to the software
Inline IDS can block some attacks, but it is signature-based and less precise than an application-aware firewall.
It does not reduce attack surface; it merely attempts to detect/block known exploits. EOL software remains fully exposed.
Reference:
CompTIA CAS-005 Exam Objectives — Domain 2: Security Operations (Attack Surface Reduction, Compensating Controls). NIST SP 800-41 (Guidelines on Firewalls and Firewall Policy) — application-aware firewalls reduce exposure. CIS Critical Security Control #12 (Boundary Defense) — restrict unneeded protocols.
Which of the following most likely explains the reason a security engineer replaced ECC with a lattice-based cryptographic technique?
A. It is computationally efficient and provides perfect forward secrecy.
B. It is more resilient to brute-force attacks than ECC.
C. It supports ephemeral key exchange and digital signatures.
D. It is currently considered a robust PQC technique.
E. It enables processing on data while remaining in an encrypted state.
Explanation:
The question contrasts ECC (elliptic curve cryptography) with lattice‑based cryptography. Lattice‑based methods are a leading family of post‑quantum cryptography (PQC) algorithms because they resist attacks from both classical and quantum computers. ECC is vulnerable to Shor’s algorithm on a sufficiently powerful quantum computer, so a security engineer would replace ECC with lattice‑based crypto primarily for quantum resistance.
Correct Option:
D. It is currently considered a robust PQC technique.
Lattice‑based cryptography (e.g., CRYSTALS‑Kyber, Falcon, Dilithium) is a finalist in NIST’s PQC standardization project.
It is believed to be secure against quantum computer attacks, whereas ECC is not.
Replacing ECC with lattice‑based crypto is a proactive migration to post‑quantum resilience.
This is the most likely driver for such a replacement in a forward‑looking security architecture.
Incorrect Options:
A. It is computationally efficient and provides perfect forward secrecy.
Lattice‑based schemes are generally less computationally efficient than ECC, not more.
Perfect forward secrecy (PFS) is a property of key exchange protocols (e.g., TLS with ephemeral keys), not inherent to a cryptographic family. ECC can also provide PFS via ECDHE.
B. It is more resilient to brute‑force attacks than ECC.
Brute‑force resistance depends on key length, not the mathematical family alone. A sufficiently long ECC key can resist classical brute‑force. The real quantum threat is not brute‑force but Shor’s algorithm, which ECC cannot resist.
C. It supports ephemeral key exchange and digital signatures.
ECC also supports ephemeral key exchange (ECDHE) and digital signatures (ECDSA, EdDSA). This is not unique to lattice cryptography and does not explain replacement.
E. It enables processing on data while remaining in an encrypted state.
That describes homomorphic encryption, which can be built on lattices but is not a property of all lattice‑based techniques. The question does not mention homomorphic requirements. Most lattice PQC (Kyber, Dilithium) does not provide homomorphic encryption.
Reference:
CompTIA CAS-005 Exam Objectives — Domain 1: Security Architecture (Cryptography — Post‑Quantum Cryptography). NIST IR 8309 (Status Report on the Third Round of the NIST PQC Standardization Process). “Lattice‑based cryptography is a leading candidate for PQC due to resistance to quantum attacks.”
A company recently acquired a manufacturing plant. The acquiring company plans to create a unified network that does not impact its security posture. The manufacturing plant has been in operation for more than 30 years and has not followed an equipment replacement life cycle. Which of the following is the best way to meet this objective?
A. Implementing a WAF and patching the legacy IT equipment
B. Extending an SD-WAN with specific policies
C. Using a site-to-site VPN and integrating the manufacturing plant into the SIEM
D. Deploying a proxy server at the manufacturing plant
Explanation:
The manufacturing plant has legacy equipment (30+ years old) with no replacement life cycle, meaning it likely cannot run modern security agents or patches. The acquiring company needs network unification without compromising security posture. An SD‑WAN with specific policies allows secure segmentation, traffic inspection, and policy-based routing without requiring changes to the legacy equipment itself.
Correct Option:
B. Extending an SD-WAN with specific policies
SD‑WAN can create logical separation between the corporate and manufacturing networks while enabling connectivity.
Specific policies (e.g., micro-segmentation, application‑aware routing) restrict traffic to only necessary protocols and destinations.
Legacy equipment remains untouched, as policies are enforced at the SD‑WAN edge.
This preserves security posture by preventing lateral movement from potentially vulnerable OT devices.
Incorrect Options:
A. Implementing a WAF and patching the legacy IT equipment
Legacy OT equipment often cannot be patched (vendor no longer supports it, or patches break functionality).
WAF protects web applications, but manufacturing systems typically use proprietary OT protocols (e.g., Modbus, Profinet), not HTTP.
This approach is impractical and may disrupt operations.
C. Using a site-to-site VPN and integrating the manufacturing plant into the SIEM
Site‑to‑site VPN connects networks but does not provide granular policy enforcement or segmentation.
Integrating legacy equipment into a SIEM requires logging capabilities that old systems usually lack.
Without access controls, the VPN could expose the corporate network to unpatched OT devices.
D. Deploying a proxy server at the manufacturing plant
A proxy forwards web traffic but does not handle OT protocols or provide network segmentation.
It adds minimal security for legacy manufacturing systems and does not address the unification objective.
Attackers can bypass a proxy if direct IP routing exists between networks.
Reference:
CompTIA CAS-005 Exam Objectives — Domain 2: Security Operations (OT/IoT Security, Network Segmentation). NIST SP 800‑82 (Guide to Industrial Control Systems Security) — recommends using firewalls or SD‑WAN to segment legacy OT networks. CISA Best Practices for Legacy OT Equipment — “Segmentation and policy enforcement at the network edge are preferred over attempting to patch unsupported systems.”
A threat intelligence company's business objective is to allow customers to integrate data
directly to different TIPs through an API. The company would like to address as many of
the following objectives as possible:
• Reduce compute spend as much as possible.
• Ensure availability for all users.
• Reduce the potential attack surface.
• Ensure the integrity of the data provided.
Which of the following should the company consider to best meet the objectives?
A. Configuring a unique API secret key for accounts
B. Publishing a list of IoCs on a public directory
C. Implementing rate limiting for each registered user
D. Providing a hash of all data that is made available
Explanation:
The company must meet four objectives: reduce compute spend, ensure availability, reduce attack surface, and ensure data integrity. Providing a hash of all data allows customers to verify that the data received via the API has not been tampered with (integrity). Hashes are computationally light, do not impact availability significantly, and add minimal attack surface compared to other controls.
Correct Option:
D. Providing a hash of all data that is made available
A hash (e.g., SHA-256) ensures data integrity by allowing clients to detect unauthorized modification.
Compute cost is low (hashing is fast), preserving the "reduce compute spend" objective.
Does not introduce authentication complexity or statefulness, thus maintaining availability.
Attack surface increase is negligible (simply serving an additional hash value).
This directly addresses integrity without conflicting with other objectives.
Incorrect Options:
A. Configuring a unique API secret key for accounts
Unique keys improve authentication and reduce attack surface by preventing unauthorized access.
However, they introduce overhead (key management, rotation, storage) and can impact compute spend (validation).
Keys do not ensure data integrity; they only authenticate the client. The data itself could still be altered in transit.
B. Publishing a list of IoCs on a public directory
Public IoC lists reduce compute spend (no per‑request processing) but increase attack surface (exposes threat intelligence to adversaries).
Availability remains high, but integrity is not ensured — anyone could modify the public directory.
This conflicts with "reduce attack surface" because adversaries see defensive indicators.
C. Implementing rate limiting for each registered user
Rate limiting protects availability and compute spend (prevents abuse).
However, it does nothing for data integrity. Attack surface reduction is minimal.
Rate limiting is a good operational control but does not meet the integrity requirement at all.
Reference:
CompTIA CAS-005 Exam Objectives — Domain 1: Security Architecture (Integrity Controls). Domain 3: Security Operations (Threat Intelligence Sharing). NIST SP 800-107 (Recommendation for Applications Using Approved Hash Algorithms) — hashes provide integrity verification. ISO/IEC 27040 (Storage security) — hashing for integrity.
As part of a security audit in the software development life cycle, a product manager must demonstrate and provide evidence of a complete representation of the code and modules used within the production-deployed application prior to the build. Which of the following best provides the required evidence?
A. Software composition analysis
B. Runtime application inspection
C. Static application security testing
D. Interactive application security testing
Explanation:
The product manager needs evidence of a complete representation of code and modules (including third‑party and open‑source components) prior to the build. This means identifying all libraries, dependencies, and components before the application is compiled or deployed. Software composition analysis (SCA) is specifically designed for this purpose.
Correct Option:
A. Software composition analysis
SCA scans project manifests, lock files, and source code to list all open‑source and third‑party components.
It identifies libraries, versions, licenses, and known vulnerabilities before build.
Provides a complete bill of materials (SBOM) as evidence for audit.
Integrates into the CI/CD pipeline pre‑build, catching issues early in the SDLC.
Incorrect Options:
B. Runtime application inspection
This analyzes a running application, not pre‑build. It cannot provide complete component representation before deployment.
Some components (e.g., unreachable libraries) may not be detected at runtime.
Does not meet the "prior to build" requirement.
C. Static application security testing
SAST analyzes source code for custom code vulnerabilities (e.g., SQL injection, buffer overflows).
It does not focus on third‑party modules or dependency inventory.
While valuable for security, it does not provide a complete representation of all used modules (especially binary libraries).
D. Interactive application security testing
IAST combines SAST and DAST by instrumenting the running application.
Like runtime inspection, it requires the application to be built and executed.
Cannot provide pre‑build evidence of modules and dependencies.
Reference:
CompTIA CAS-005 Exam Objectives — Domain 2: Security Operations (Software Assurance / DevSecOps). NIST SSDF (Secure Software Development Framework) — PO.1: “Identify and manage software components.” OWASP SCA (Software Composition Analysis) — generates SBOM.
A security administrator needs to review the efficacy of the detection rules configured on the SIEM by employing real-world attacker TTPs. Which of the following actions should the security administrator take to accomplish this objective?
A. Perform an internal penetration test.
B. Use adversary emulation.
C. Execute an internal vulnerability assessment.
D. Perform a threat hunt exercise.
E. Ingest new threat intelligence feeds.
Explanation:
The objective is to review detection rule efficacy using real-world attacker TTPs (tactics, techniques, and procedures). Adversary emulation mimics specific threat actor behaviors based on frameworks like MITRE ATT&CK. Unlike a penetration test, which focuses on exploitation and achieving a goal, adversary emulation tests whether the SIEM detects known adversary behaviors.
Correct Option:
B. Use adversary emulation.
Adversary emulation simulates a specific threat actor's TTPs (e.g., APT29, FIN7) using documented behavior patterns.
It directly tests whether SIEM detection rules fire against those real-world techniques.
Results show gaps in detection coverage and rule efficacy.
This is more targeted than penetration testing for validating detection, not just prevention or exploitation.
Incorrect Options:
A. Perform an internal penetration test.
Penetration testing focuses on exploiting vulnerabilities to gain access or achieve a specific objective.
It does not systematically test detection rules against a range of TTPs.
Attackers may use custom or limited methods, not representative of real-world adversary behavior sets.
C. Execute an internal vulnerability assessment.
Vulnerability assessment identifies missing patches, weak configurations, etc.
It does not execute attacks or simulate TTPs.
Unrelated to testing SIEM detection rule efficacy.
D. Perform a threat hunt exercise.
Threat hunting assumes detection already exists and proactively searches for signs of compromise.
It does not introduce attacker TTPs to test detection rules.
Relies on existing telemetry and hypotheses, not active emulation.
E. Ingest new threat intelligence feeds.
TI feeds provide information about indicators and TTPs but do not execute those TTPs.
Without going emulation, the administrator cannot verify if new intelligence translates to detection rule coverage.
Passive intake does not test rule efficacy.
Reference:
CompTIA CAS-005 Exam Objectives — Domain 3: Security Operations (Threat Hunting, Adversary Emulation). MITRE ATT&CK Framework — "Adversary emulation is a method for testing defenses using real-world TTPs." NIST SP 800-53 (CA-8: Penetration Testing vs. Adversary Emulation distinction).
| Page 11 out of 36 Pages |
