Free CompTIA PK0-005 Practice Questions 2026 - Page 10
A PM is working to establish accepted communication channels and to define access requirements. In which of the following phases is the project?
A. Discovery
B. Execution
C. Initiating
D. Planning
Explanation:
During the Planning phase, the project manager defines how the project will be executed, monitored, and controlled. This includes establishing project processes such as:
Communication channels and communication plans
Access requirements for systems, tools, and information
Resource planning
Risk planning
Schedule and scope planning
Since the PM is defining communication methods and determining who has access to project resources, these activities are part of developing the project management plan, which occurs in the Planning phase.
❌ Why the other options are incorrect:
A. Discovery
Discovery focuses on gathering initial requirements and understanding the problem or opportunity, not defining communication channels.
B. Execution
In execution, the team performs the planned work. Communication channels should already be established before this phase begins.
C. Initiating
Initiating focuses on authorizing the project and identifying stakeholders (e.g., creating the project charter). Detailed communication planning typically happens afterward.
📚 PK0-005 Reference:
Domain 1 – Project Management Concepts / Project Life Cycle
Planning phase
Communication management planning
💡 Exam Tip:
If the question mentions creating plans, defining processes, or setting communication rules, it almost always refers to the Planning phase.
A procurement team analyzes solutions submitted from multiple vendors for the upcoming release of a required development service. The procurement team identifies a potential partnership. Which of the following would the procurement team most likely request?
A. Quote
B. Information
C. Proposal
D. Bid
Explanation:
The question describes the procurement team analyzing solutions submitted from multiple vendors for a development service. They are looking at the vendors' approaches, not just prices. The key word is "solutions," which indicates that the vendors have been asked how they would approach the work.
Why C is correct:
A Request for Proposal (RFP) is used when the buyer wants vendors to propose a solution to a problem or a detailed approach to delivering a service. An RFP asks for more than just a price; it asks for a methodology, timeline, qualifications, and approach. Since the team is analyzing "solutions" and sees a potential partnership, they are likely reviewing proposals submitted in response to an RFP.
Why A is incorrect:
A quote is typically requested via an RFQ (Request for Quote) when the requirements are very specific and the buyer is primarily looking for a price (e.g., for standard, off-the-shelf items). Development services usually require a proposal, not just a quote.
Why B is incorrect:
A Request for Information (RFI) is used to gather general information about vendor capabilities and market options, not to solicit formal solutions for a specific upcoming release. An RFI is typically done before an RFP.
Why D is incorrect:
A bid (solicited via an IFB - Invitation for Bid) is used when the requirements are clear and the primary deciding factor is price. This is not suitable for a development service where the solution approach matters.
References:
CompTIA Project+ PK0-005 Objective 2.5: Given a scenario, use the appropriate procurement documentation. This objective covers the differences between RFI (information), RFP (proposal/solution), and RFQ/IFB (price/quote).
Procurement Documents:
RFI: Used to gather information.
RFP: Used to solicit proposals (solutions).
RFQ/IFB: Used to solicit quotes/bids (prices).
Which of the following should be considered first when determining the privacy management for project data?
A. Evaluating the current privacy protection program
B. Understanding applicable privacy regulations
C. Maintaining awareness of industry best practices
D. Implementing security role-based controls
Explanation:
When determining how to manage the privacy of project data, legal and regulatory requirements must always be the starting point. These regulations set the mandatory "floor" for what you can and cannot do with data.
Compliance:
Before you can design a program or implement controls, you must know which laws apply (e.g., GDPR in Europe, CCPA in California, HIPAA for healthcare). Failure to comply with these can lead to massive fines and project termination.
Geographic Scope:
Regulations often depend on where the data is stored or where the users reside.
Data Classification:
Regulations will define what constitutes "Personally Identifiable Information" (PII), which then dictates the level of privacy management required.
Explanation of Incorrect Answers
A. Evaluating the current privacy protection program:
While useful, you cannot effectively evaluate an existing program until you know the legal standards (regulations) it is supposed to be measured against.
C. Maintaining awareness of industry best practices:
Best practices are "nice-to-have" or optimal ways of working, but regulations are legal requirements. Laws always take precedence over best practices.
D. Implementing security role-based controls:
This is a technical solution that occurs during the implementation phase. You cannot decide how to restrict access until you understand what the law requires you to protect.
References
CompTIA Project+ (PK0-005) Exam Objectives: Domain 2.0 Project Planning (2.1 Explain the importance of project-planning documents – Privacy and Security requirements).
PMBOK® Guide: Section on Project Environment – Regulatory and Legal requirements.
A project manager distributes minutes after each project meeting. However, the project manager is having difficulties hosting the meetings and documenting the discussions simultaneously. Which of the following should the project manager do in order to be most efficient?
A. Assign a scribe to take notes.
B. Record the meeting and transcribe the notes later.
C. Instruct each team member to take notes.
D. Get a facilitator for the meetings.
Explanation:
In the CompTIA Project+ PK0-005 exam objectives, effective meeting management and communication are key responsibilities of the project manager (Objective 1.4 – Compare and contrast communication management concepts, and Objective 2.4 – Execution phase activities, including "Conduct meetings" and "Document meeting minutes").
The scenario describes a common challenge: the project manager is trying to facilitate/host the meeting (leading discussion, keeping it on track, ensuring participation, managing time, resolving conflicts) while simultaneously documenting (taking detailed minutes). This dual role often reduces efficiency, leads to incomplete notes, missed key points, or poor meeting flow.
The most efficient solution is:
A. Assign a scribe to take notes
A scribe (also called note-taker or recorder) is a designated team member responsible solely for capturing the discussion, decisions, action items, owners, and deadlines during the meeting.
This allows the project manager to focus entirely on facilitating — guiding the agenda, encouraging input, managing time, and ensuring objectives are met — without dividing attention.
The minutes can then be reviewed quickly by the PM before distribution, ensuring accuracy and completeness.
This is a standard best practice in project management for productive meetings, especially recurring status, planning, or stand-up meetings.
Why the other options are less efficient or not the best:
B. Record the meeting and transcribe the notes later
While recording (audio/video) is useful, transcribing afterward is time-consuming (often 2–4× the meeting length), prone to errors (accents, overlapping talk, background noise), and delays distribution of minutes. It does not solve the real-time facilitation burden during the meeting itself.
C. Instruct each team member to take notes
This creates inconsistent, incomplete, and fragmented notes — each person captures different points based on their perspective. It leads to confusion, duplicated effort, and no single reliable source of truth. Minutes still require consolidation, defeating efficiency.
D. Get a facilitator for the meetings
A separate facilitator can help run the meeting smoothly (especially for complex or contentious discussions), but it does not directly address the documentation challenge. The PM would still need to handle minutes or assign someone else, adding overhead (and cost) without solving the dual-role problem as cleanly as a scribe.
Reference:
PK0-005 Objective 1.4 – Communication tools and techniques, which includes assigning roles such as scribe for meetings; Objective 3.2 – Productivity tools, where meeting documentation is emphasized; and widely covered in CompTIA Project+ study guides as a way to improve meeting efficiency.
During the stabilization phase for recently deployed software, an end user reports a bug that is compromising data integrity. Which of the following tools will the project manager MOST likely use?
A. Issue log
B. Defect log
C. Change log
D. Task board
Explanation:
During the stabilization phase of deployed software, when an end user reports a bug compromising data integrity, the project manager should use the defect log. This log is specifically designed to track software bugs, their severity, and resolution status.
A. Issue log:
Tracks general project issues (e.g., resource conflicts, risks realized), but not technical defects in software.
B. Defect log:
✅ Correct. Used to record, monitor, and manage bugs found during testing or stabilization.
C. Change log:
Records approved changes to scope, schedule, or budget, not defects.
D. Task board:
Visualizes ongoing work items, but not defect tracking.
💡 Exam Tip:
Defect log = bugs/errors in software
Issue log = project-level problems
Change log = approved modifications
Task board = work progress visualization
Several stakeholders have declined the invitation for the kickoff of a major digital transformation protect. Which of the following actions should the project manager take NEXT?
A. Escalate directly to the project sponsor
B. Push the kickoff meeting out by one week
C. Proceed with the kickoff as planned
D. Identity replacements for project stakeholders
Explanation:
✅ Escalate to the sponsor: The project sponsor is the person who provides the authority, funding, and overall support for the project. For a "major digital transformation," the absence of multiple stakeholders at the kickoff meeting significantly risks alignment on vision and scope. The sponsor has the organizational influence to engage these stakeholders and ensure their participation is prioritized.
Why the other options are incorrect:
❌ B. Push the kickoff meeting out by one week:
Delaying the meeting without addressing the root cause (why they declined) often just leads to further delays without guaranteed attendance.
❌ C. Proceed with the kickoff as planned:
While sometimes an option for minor projects, proceeding with a major digital transformation without key stakeholders misses the primary purpose of the kickoff: establishing buy-in and shared understanding. This would likely lead to rework and communication failures later.
❌ D. Identify replacements for project stakeholders:
Stakeholders are usually assigned based on their role and authority within the organization. A project manager generally does not have the power to arbitrarily replace them; this is a decision for higher management or the sponsor.
Given the following velocity chart:
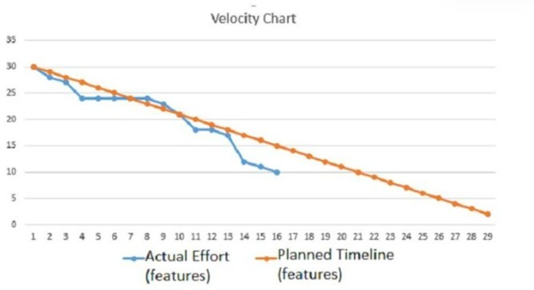
Which of the following updates on the project status should the Scrum master provide to the senior management team?
A. The project utilized all of its available reserve.
B. The project has scope creep.
C. The project deviated from the critical path.
D. The project is trending ahead of schedule.
Explanation:
The chart shows two lines:
Orange line: Planned timeline (planned feature completion)
Blue line: Actual effort (actual features remaining)
In Agile charts like this (similar to a burndown/velocity comparison), when the actual line falls below the planned line, it means the team is completing work faster than planned.
From about iteration 4 onward, the actual effort line is consistently below the planned line, meaning:
Fewer features remain than expected
Work is being completed faster than planned
The team is ahead of schedule
Therefore, the Scrum master should report that the project is trending ahead of schedule.
❌ Why the other options are incorrect:
A. The project utilized all of its available reserve:
The chart shows work progress, not contingency or reserve usage.
B. The project has scope creep:
Scope creep would typically show more work being added or the remaining work increasing, which is not happening here.
C. The project deviated from the critical path:
The critical path is a concept from traditional (Waterfall) scheduling, not Agile velocity tracking.
📚 PK0-005 Reference:
Domain 2 – Project Management Concepts / Agile Metrics
Velocity tracking
Burn charts and progress monitoring
💡 Exam Tip:
On Project+ Agile charts:
Actual line below planned → ahead of schedule
Actual line above planned → behind schedule
Hackers are attempting to extract large amounts of data to sell on the dark web. Which of the following steps should a project manager take next to mitigate this risk?
A. Update the issue log.
B. Apply the contingency plan.
C. Transfer the risk.
D. Submit a change request.
Explanation:
✅ Apply the contingency plan: When a risk—such as a hacking attempt—is imminent or currently occurring, the project manager must immediately execute the predefined response strategy designed to mitigate the impact. In this context, a contingency plan often includes technical actions like isolating affected systems, activating incident response teams, or deploying emergency security controls to stop the data extraction.
Why the other options are incorrect:
❌ A. Update the issue log:
While the hack is indeed an issue, updating the log is an administrative recording task. During an active attack, the priority is taking action to protect data (Option B) rather than just documenting the event.
❌ C. Transfer the risk:
Risk transfer (e.g., buying insurance or outsourcing) is a planning-phase strategy. You cannot "transfer" the risk once the attack has already begun to prevent the immediate loss of data.
❌ D. Submit a change request:
A change request is used to modify project baselines. While a security overhaul might require a change request after the incident is resolved, it is not an emergency response tool to stop an ongoing theft.
A critical business initiative introduced new processes and technology to the organization. Which of the following approaches should be used to ensure the deliverables are increasingly adopted and leveraged by the organization over time?
A. Creation of a social news forum
B. Management directives to use the new system
C. New user kickoff meeting
D. Monthly feedback and training sessions
Explanation:
The question focuses on ensuring that new processes and technology are increasingly adopted and leveraged by the organization over time. This is about long-term change management and user adoption, not just a one-time event.
Why D is correct:
Monthly feedback and training sessions provide ongoing support, reinforcement, and opportunities for users to learn and improve their skills. This continuous engagement helps users become more comfortable and proficient with the new system, leading to increased adoption and leveraging of the technology over time. It addresses the "over time" aspect of the question by providing sustained support.
Why A is incorrect:
A social news forum might facilitate communication among users, but it is passive and does not provide structured training or feedback mechanisms. It alone will not drive increasing adoption.
Why B is incorrect:
Management directives (forcing people to use the system) can mandate initial use, but they do not ensure that users will leverage the system effectively or adopt it willingly over time. Mandates often lead to resistance, not increasing proficiency.
Why C is incorrect:
A new user kickoff meeting is a good initial training and awareness event, but it is a one-time activity. It does not provide the ongoing support needed to ensure increasing adoption over time. Users need continued help as they encounter challenges.
References:
CompTIA Project+ PK0-005 Objective 4.2: Explain the importance of knowledge transfer and closeout activities. This objective covers the concept of transitioning deliverables to operations and ensuring ongoing support and training for long-term adoption.
Organizational Change Management: Successful adoption of new processes and technology requires ongoing reinforcement, training, and support, not just a single launch event. This is often part of the project's transition to operations.
During a complex, multiyear project, a PM must discern which project tasks overlap so resources can be allocated appropriately. Which of the following is best for determining this information?
A. PERT chart
B. Milestone chart
C. Gantt chart
D. Budget burndown chart
Explanation:
A Gantt chart is the premier tool for visualizing a project schedule. It uses horizontal bars to represent the duration of tasks against a timeline. It is the "best" tool for discerning overlapping tasks because:
Visual Overlap:
You can see exactly which bars (tasks) occupy the same dates on the horizontal axis. This makes it easy to identify periods where multiple tasks are happening simultaneously.
Resource Allocation:
By seeing the overlaps, a PM can identify "Resource Over-allocation" (e.g., if one person is assigned to three overlapping tasks) and perform Resource Leveling.
Dependencies:
Most Gantt charts show arrows (lines) between tasks, indicating Finish-to-Start or Start-to-Start relationships, which further clarifies why tasks are overlapping.
Explanation of Incorrect Answers
A. PERT chart (Program Evaluation and Review Technique):
A PERT chart is a network diagram that focuses on the logic and flow of tasks. While it shows dependencies and the critical path, it does not display tasks against a calendar or timeline, making it very difficult to visually "see" the exact dates where tasks overlap.
B. Milestone chart:
This chart only shows major events or deliverables (points in time). It does not show the duration of tasks (the bars), so it is impossible to determine if the work leading up to those milestones is overlapping.
D. Budget burndown chart:
This is a financial tracking tool. It shows how much of the budget has been spent over time. It provides no information about specific task schedules or resource assignments.
References:
CompTIA Project+ (PK0-005) Exam Objectives: Domain 2.0 Project Planning (2.2 Explain the purpose and use of common project-management tools – Gantt charts).
PMBOK® Guide: Section on Project Schedule Management – Bar Charts (Gantt Charts).
| Page 10 out of 44 Pages |
